- Photonics Research
- Vol. 10, Issue 7, 1703 (2022)
Abstract
1. INTRODUCTION
Since the BB84 protocol was proposed in 1984 [1], quantum key distribution (QKD) has been studied for so many years in both theories and experiments [2–6]. The decoy-state BB84 protocol [7–9] was widely used in the experiments [10–14] and QKD networks [15–17] in which the decoy-state method can ensure the security of QKD with imperfect single-photon sources. Recently, an integrated space-to-ground quantum communication network over 4600 km was demonstrated by applying the decoy-state BB84 protocol [18]. But, in principle, the detectors in the BB84 protocol could be hacked by an eavesdropper due to the imperfections of the detectors [19,20]. Although there are some defense strategies against known attacks, we need a more robust method to protect the security with imperfect detectors.
Based on the virtual entanglement swapping, measurement-device-independent (MDI)-QKD protocol [21,22] can repair all the detection side vulnerabilities. The three-intensity MDI-QKD protocol [23–25] can ensure the security with both imperfect single-photon sources and detectors, but the key rate is pretty low. Many improved schemes were proposed to increase the key rate [26–29]. Among all those, the four-intensity MDI-QKD protocol [29] can improve the key rate by several orders of magnitude and becomes the mainstream of MDI-QKD protocol. The four-intensity MDI-QKD protocol has been applied to the experiments of long-distance MDI-QKD [30], free-space MDI-QKD [31], chip-based MDI-QKD [32–34], high-speed MDI-QKD [35], and so on [36,37]. Based on the four-intensity MDI-QKD protocol [29], we proposed a double-scanning method [38], which can further improve the key rate by up to 280% in typical experiment conditions. The double-scanning method [38] with four-intensity MDI-QKD protocol has been applied in a recent experiment [39].
Recently, based on single-photon interference, twin-field (TF)-QKD [40] was proposed. The TF-QKD can raise the key rate from the linear scale to square root scale of channel transmittance and break the PLOB bound [41], the key rate limit of repeaterless QKD. TF-QKD protocol and its variants [42–45] have been widely studied in theories [46–51] and experiments [52–57]. Specially, sending-or-not-sending (SNS) TF-QKD [42] has been realized in the 428 km field experiment [58], the 511 km field experiment [59], and the 605 km laboratory experiment [60], which are the farthest field experiments and laboratory experiment to date.
Sign up for Photonics Research TOC. Get the latest issue of Photonics Research delivered right to you!Sign up now
One significant technique in TF QKD protocols is phase post-selection, which can reduce the phase-error or bit-error in the interference. In this paper, we propose a modified MDI-QKD protocol with phase post-selection to improve the key rate by reducing the estimated phase-error rate. The paper is arranged as follows. We first introduce the main idea of our modified protocol and prove its security. Then we show some numerical results to compare the modified protocol with other protocols. The paper is ended with concluding remarks.
2. PROTOCOL
Based on the decoy-state MDI-QKD protocol, we propose a modified protocol with phase post-selection. We assume Alice and Bob take the weak coherent state (WCS) sources to encode the quantum signals. The state of a WCS pulse with intensity and phase is denoted by
A. Main Idea
In the th time window, Alice (Bob) sends out a strong reference pulse followed by a signal pulse in state to the untrusted third-party Charlie, where and represent the public phase related to the strong reference pulse, and and represent the private phase. The public phases are known to everyone, and the private phases are randomly selected from . Some of the private phases are announced in the data post-processing, and the other private phases are never announced in the whole protocol.
For the received signal pulse pairs, Charlie is assumed to first compensate for the difference in public phases and then perform the Bell measurement. In this protocol, we will make post-selection for a set of signal pulse pairs in basis. We make the post-selection according to the difference between the private phases of the pulse pair. The goal of this post-selection is to make the observed error rate in subset be small enough so as to make a better estimation for the phase-flip error rate of single-photon pairs in basis. For this goal, we need a small positive value in the following formula:
As we shall show later, such a post-selection can produce a smaller observed phase-flip error rate for the single-photon pairs if is small. Before going further, we first show the idea in more details by the example of the four-intensity protocol [29,38].
We shall post-select a subset of pulse pairs . By using results of all pulse pairs in basis, we can evaluate the yield of the single-photon pairs, which can be used to obtain the yield of all single-photon pairs and also the yield of the single-photon pairs in set only. Then, to calculate the final key rate, we have two options. One is to ignore the subset and just calculate the key rate using the standard method of the four-intensity protocol. The other is to use the observed error rate in subset , then estimate the phase-flip error rate for single-photon pairs in basis, and finally calculate the final key rate by this. We will always choose the one that produces the higher key rate. A small results in a small observed error rate in subset , but the number of observed error events will also be small, which would cause large statistical fluctuations. Thus, there is a trade-off between the observed error rate and the number of observed error events, and we need to optimize to achieve the best estimation of the phase-flip error rate.
B. Implementation Process of the Protocol
We take the four-intensity MDI-QKD protocol with phase post-selection to show the whole implementation process.
There are four WCS sources with different intensities at Alice’s and Bob’s sides, respectively. In basis, Alice (Bob) uses WCS sources , , and (, , and ) with intensities , , and (, , and ), respectively. In basis, Alice (Bob) uses WCS source () with intensity (). In the th time window, Alice (Bob) randomly prepares a signal pulse in state with probability () for , where and are randomly selected from . The signal pulse is encoded in basis if and in basis if . Then Alice (Bob) sends out the prepared signal pulse to Charlie. Charlie is assumed to first compensate for the difference in public phases, and then perform the Bell measurement to the received pulse pairs. Charlie announces the outcome to Alice and Bob. If two specific detectors click (for example, two and only two detectors corresponding to different polarizations click in the polarization coding scheme), Alice and Bob take it as an effective event, and Alice and Bob only keep the data of effective events.
To efficiently estimate the difference in public phases of the pulse pairs received in Charlie’s detectors, the method performed in the TF-QKD experiments can be applied here [52–57]. Alice (Bob) encodes the strong reference pulses multiplexed with the signal pulses by modulating a continuous light into pulsed light. The signal pulses are quantum signals with random phases and single photon level intensities, while the strong reference pulses are classical signals with fixed phases and usually more than dozens to hundreds of times stronger than intensity of the signal pulses. Based on the recorded interference results of the strong reference pulses, Charlie can accurately estimate the relative difference in public phases of the received signal pulse pairs.
After Alice and Bob repeat the above process for times and Charlie announces all the outcomes, they (Alice and Bob) acquire a series of data. Then, Alice and Bob first announce the intensity of the pulse corresponding to each effective event. For the effective events that both Alice and Bob take the sources, they then announce the private phases and . The private phases of other effective events are never announced. We denote as the pulse pair source if Alice takes the source and Bob takes the source for . We use the following criteria for the effective events of the source to make post-selection for the subset :
3. SECURITY PROOF
Since only the private phases of the effective events of the source are revealed in this protocol, we only need to consider the security of those parts. For simplicity, we first consider the following virtual protocol.
For virtual protocol, to each pulse pair of the source, only Alice and Bob know the value , but they do not know the phase values . Here we choose the region in our discussion. Therefore, the density operator of a signal pulse pair from any subset from whatever post-selection strategies that satisfy Eq. (3) can be written as
Doing the integration in Eq. (4), we find that the density operator can be decomposed in the following convex form:
Hence, we have Lemma 1. For a pulse pair from any post-selected subset , it can be regarded as the classical mixture of a single-photon pair with probability and another density operator with probability .
Obviously, even Alice and Bob know the values of and , but they never use the information of values of and ; a pulse pair from subset can still be regarded as the classical mixture of a single-photon pair with probability and another density operator with probability . We define as the set of single-photon pulse pairs from Q. Since in the distribution process no one can tell the difference between the pulse pairs from and the ideal single-photon pulse pairs in basis, we have the following. (1) The yield of single-photon pulse pairs calculated from all effective events caused by pulse pairs in basis is asymptotically equal to the yield of single-photon pulse pairs from set . (2) The bit-flip error rate of the effective events of single-photon pulse pairs from is asymptotically equal to the phase-flip error rate of all those effective events caused by single-photon pairs prepared in basis.
In the real protocol, Alice and Bob cannot know the values of each of the pulse pair from source before the private phases are announced. But if they announce the private phases through a secret channel that cannot be eavesdropped by anyone else, the above discussion still holds. In the following, we shall prove that the security of Alice and Bob’s announcing the private phases through a private channel is equivalent to that of announcing the private phases through a public channel.
The private phases of the pulse pairs from basis are never announced; thus, those pulse pairs are the classical mixture of Fock states. To calculate the final key rate, we need to know the lower bound of the number of the effective events caused by single-photon pairs from basis and the upper bound of its corresponding phase-flip error rate . Note the values of and are objective facts, which do not change by any outside information when the quantum distribution process of the protocol is done and Charlie has announced all detection outcomes. This is to say, after Alice and Bob know this fact, they can announce the private phases of all pulse pairs from source, and this does not affect the security of the protocol. We suppose Alice and Bob get the values of and through a secret channel, and get the lower bound of the number of the effective events caused by single photon pairs from basis and the upper bound of its corresponding phase-flip error rate through a public channel. Since all observed values are the same in the case of secret channel and public channel, we have and . This ends the proof.
4. KEY RATE FORMULA
The phase post-selection method can be combined with both the single-scanning method [29] and the double-scanning method [38] of the four-intensity MDI-QKD protocol. Here we take the phase post-selection method combined with the double-scanning method as an example to show the calculation method of the final key rate. The method can be easily generalized to the case of combining with the single-scanning method.
As discussed in Section 3, the phase post-selection does not affect the security; thus, the density matrix of the pulse pairs from source can still be regarded as the classical mixture of Fock states. We denote the density matrix of source by
According to the data in basis, Alice and Bob get the observed value of the number of effective events of source , . We denote the expected value of by . With Chernoff bound [61], we can estimate the expected value according to the observed value. We denote the estimated lower and upper bounds of the expected value by the superscripts and , respectively. Besides, we denote the number of wrong effective events of source as whose corresponding expected value is .
With Eqs. (4)–(6), we can get the density matrix of the pulse pairs from set ,
As shown in Ref. [38], if , the lower bound of the expected value of the yield of the single-photon pulse pairs is
The upper bound of the expected value of the phase-flip error rate of the single-photon pairs from basis is
As discussed in Section 3, we can use the observed value in set to get . Let satisfy
Since both Eqs. (15) and (17) are the upper bounds of the expected value of the phase-flip error rate, we can always use the smaller one to be the estimated upper bound. This is to say, for each group , we apply Eq. (11) to calculate , and we have
With the Chernoff bound, we can get the real value of the lower bound of the yield of the single-photon pulse pairs from source , , and its corresponding upper bound of the phase-flip error rate, ,
Then we have
5. NUMERICAL SIMULATION
We shall show the advantage of phase post-selection through the numerical simulation results. Similar to prior art works, we take linear model for channel transmittance [21,62] for the provably observed values of and in our simulation. The simulation method of is shown in Appendix B. The experiment parameters are listed in Table 1. In the optimization of the phase post-selection combined with the double-scanning method, except for the source parameters, is also a parameter to be optimized. List of Experimental Parameters Used in Numerical Simulations Here 1.5% 40.0% 1.1 0.2
In the global parameter optimization process, if we directly scan in their range to calculate the key rate, it would be pretty time-consuming. We propose an accelerated method that can reduce the running time of the optimized program from several days to less than half an hour.
The accelerated method can reduce the scanning parameters from two to one. To clearly show this, we denote , , , and .
If , then no matter what values take, the worst case of the key rate must be achieved when .
If , then for each certain , where , the worst case of the key rate is achieved when is the smallest. With the simplest linear programming method, we can easily know that when , is the smallest, and
If , the above method is obviously correct. But for the case , we need to prove that the worst case of the key rate cannot be achieved in the range .
We denote . It is easy to check ; thus, we have . With Eq. (18), we have
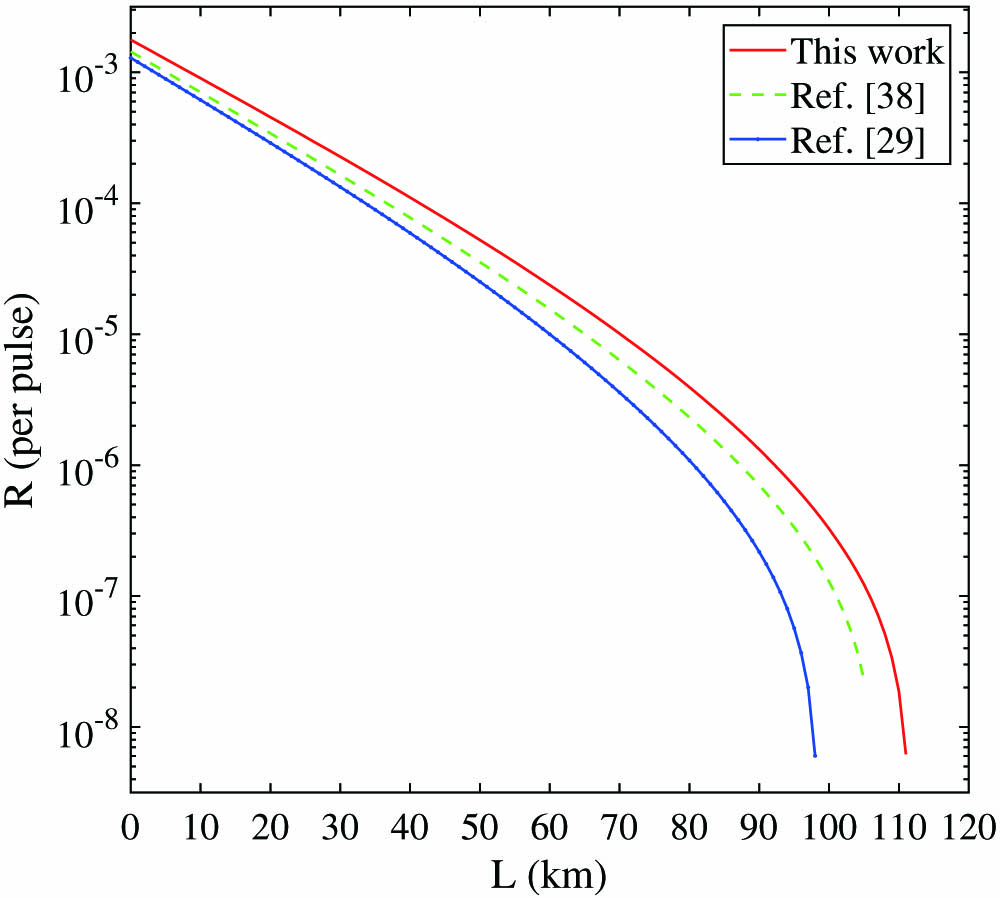
![Comparison of the key rates with this work and the former methods under the symmetric channel. The line of Ref. [38] is the key rates of the double-scanning four-intensity MDI-QKD protocol, and the line of Ref. [29] is the key rates of the original four-intensity MDI-QKD protocol. The experiment parameters are listed in Table 1.](/richHtml/prj/2022/10/7/07001703/img_001.jpg)
Figure 1.Comparison of the key rates with this work and the former methods under the symmetric channel. The line of Ref. [38] is the key rates of the double-scanning four-intensity MDI-QKD protocol, and the line of Ref. [29] is the key rates of the original four-intensity MDI-QKD protocol. The experiment parameters are listed in Table
![]()
Figure 2.Comparison of the key rates with this work and the former methods under the symmetric channels. The experiment parameters here are similar to those in Fig.
Except for the symmetric model, the method introduced in this work can be directly applied to the asymmetric channels by simply removing the constraints and . Figures 3 and 4 are the comparison of the key rates with this work and the former methods [29,38] under the asymmetric channels. In the metro QKD network, the distance of QKD is usually less than 50 km, and the maximum possible asymmetry is about 20 km. Thus, we set . The other experiment parameters of Fig. 3 are the same as those of Fig. 1, and the other experiment parameters of Fig. 4 are the same as those of Fig. 2. The results show that the method of this work can obviously improve the key rates under the asymmetric channels.
![]()
Figure 3.Comparison of the key rates with this work and the former methods under the asymmetric channels. The experiment parameters are listed in Table
![]()
Figure 4.Comparison of the key rates with this work and the former methods under the asymmetric channels. The experiment parameters here are similar to those in Fig.
![]()
Figure 5.Bell measurement setup of Charlie [21]. Here we take the polarization-encoding as an example to show the simulation method and the results of the phase-encoding are the same. BS, 50:50 beam splitter; PBS, polarization beam splitter;
Compared with the former works of MDI-QKD, the method of this work can obviously improve the key rates. But if the infinite decoy-states and infinite-key are considered, both this work and former works can accurately estimate the phase-flip error rate and the counting rate of single-photons, and thus they have similar performances in cases that are limited by the PLOB bound [5,41].
6. CONCLUSION
Based on the technique of the single-photon interference, we propose a modified MDI-QKD protocol with phase post-selection. We prove the security of the announcement of the private phases of the pulse pairs from source. We also show how to apply the phase post-selection method to the double-scanning four-intensity MDI-QKD protocol. The numerical results show that the phase post-selection method can significantly improve the key rate at all distances. In principle, our method can be directly applied to free-space MDI-QKD. But due to the atmospheric turbulence or moving sites (such as the satellite), the channel is always unstable and changes rapidly, and how to efficiently apply our method to free space will be further studied in future works.
APPENDIX A: CHERNOFF BOUND
The Chernoff bound can help us estimate the expected value from their observed values [
Besides, we can use the Chernoff bound to help us estimate their real values from their expected values. Similar to Eqs. (
APPENDIX B: THE SIMULATION METHOD OF OBSERVED VALUES IN SET Q
A typical detection set-up of Charlie is shown in Fig.
We first consider the case that the polarization of the pulse pair is in , where represents the 45° polarization, and we have
After the BS and polarization beam splitter (PBS), the state becomes
The measurement operator that and click is
With a similar method, we can conclude that the probabilities that click, click, and click:
With a similar method, we can get the probabilities that the other polarization input states cause a wrong effective event and a correct effective event are also and . Finally we have
References
[1] C. H. Bennett, G. Brassard. Quantum cryptography: public key distribution and coin tossing. Proceedings of the IEEE International Conference on Computers, Systems, and Signal Processing, 175-179(1984).
[2] N. Gisin, G. Ribordy, W. Tittel, H. Zbinden. Quantum cryptography. Rev. Mod. Phys., 74, 145-195(2002).
[3] N. Gisin, R. Thew. Quantum communication. Nat. Photonics, 1, 165-171(2007).
[4] F. Xu, X. Ma, Q. Zhang, H.-K. Lo, J.-W. Pan. Secure quantum key distribution with realistic devices. Rev. Mod. Phys., 92, 025002(2020).
[5] S. Pirandola, U. L. Andersen, L. Banchi, M. Berta, D. Bunandar, R. Colbeck, D. Englund, T. Gehring, C. Lupo, C. Ottaviani, J. Pereira, M. Razavi, J. S. Shaari, M. Tomamichel, V. C. Usenko, G. Vallone, P. Villoresi, P. Wallden. Advances in quantum cryptography. Adv. Opt. Photon., 12, 1012-1236(2020).
[6] V. Scarani, H. Bechmann-Pasquinucci, N. J. Cerf, M. Dušek, N. Lütkenhaus, M. Peev. The security of practical quantum key distribution. Rev. Mod. Phys., 81, 1301-1350(2009).
[7] W.-Y. Hwang. Quantum key distribution with high loss: toward global secure communication. Phys. Rev. Lett., 91, 057901(2003).
[8] X.-B. Wang. Beating the photon-number-splitting attack in practical quantum cryptography. Phys. Rev. Lett., 94, 230503(2005).
[9] H.-K. Lo, X. Ma, K. Chen. Decoy state quantum key distribution. Phys. Rev. Lett., 94, 230504(2005).
[10] D. Rosenberg, J. W. Harrington, P. R. Rice, P. A. Hiskett, C. G. Peterson, R. J. Hughes, A. E. Lita, S. W. Nam, J. E. Nordholt. Long-distance decoy-state quantum key distribution in optical fiber. Phys. Rev. Lett., 98, 010503(2007).
[11] T. Schmitt-Manderbach, H. Weier, M. Fürst, R. Ursin, F. Tiefenbacher, T. Scheidl, J. Perdigues, Z. Sodnik, C. Kurtsiefer, J. G. Rarity, A. Zeilinger, H. Weinfurter. Experimental demonstration of free-space decoy-state quantum key distribution over 144 km. Phys. Rev. Lett., 98, 010504(2007).
[12] C.-Z. Peng, J. Zhang, D. Yang, W.-B. Gao, H.-X. Ma, H. Yin, H.-P. Zeng, T. Yang, X.-B. Wang, J.-W. Pan. Experimental long-distance decoy-state quantum key distribution based on polarization encoding. Phys. Rev. Lett., 98, 010505(2007).
[13] A. Boaron, G. Boso, D. Rusca, C. Vulliez, C. Autebert, M. Caloz, M. Perrenoud, G. Gras, F. Bussières, M.-J. Li, D. Nolan, A. Martin, H. Zbinden. Secure quantum key distribution over 421 km of optical fiber. Phys. Rev. Lett., 121, 190502(2018).
[14] S.-K. Liao, W.-Q. Cai, W.-Y. Liu, L. Zhang, Y. Li, J.-G. Ren, J. Yin, Q. Shen, Y. Cao, Z.-P. Li, F.-Z. Li, X.-W. Chen, L.-H. Sun, J.-J. Jia, J.-C. Wu, X.-J. Jiang, J.-F. Wang, Y.-M. Huang, Q. Wang, Y.-L. Zhou, L. Deng, T. Xi, L. Ma, T. Hu, Q. Zhang, Y.-A. Chen, N.-L. Liu, X.-B. Wang, Z.-C. Zhu, C.-Y. Lu, R. Shu, C.-Z. Peng, J.-Y. Wang, J.-W. Pan. Satellite-to-ground quantum key distribution. Nature, 549, 43-47(2017).
[15] M. Peev, C. Pacher, R. Alléaume, C. Barreiro, J. Bouda, W. Boxleitner, T. Debuisschert, E. Diamanti, M. Dianati, J. F. Dynes, S. Fasel, S. Fossier, M. Fürst, J.-D. Gautier, O. Gay, N. Gisin, P. Grangier, A. Happe, Y. Hasani, M. Hentschel, H. Hübel, G. Humer, T. Länger, M. Legré, R. Lieger, J. Lodewyck, T. Lorünser, N. Lütkenhaus, A. Marhold, T. Matyus, O. Maurhart, L. Monat, S. Nauerth, J.-B. Page, A. Poppe, E. Querasser, G. Ribordy, S. Robyr, L. Salvail, A. W. Sharpe, A. J. Shields, D. Stucki, M. Suda, C. Tamas, T. Themel, R. T. Thew, Y. Thoma, A. Treiber, P. Trinkler, R. Tualle-Brouri, F. Vannel, N. Walenta, H. Weier, H. Weinfurter, I. Wimberger, Z. L. Yuan, H. Zbinden, A. Zeilinger. The SECOQC quantum key distribution network in Vienna. New J. Phys., 11, 075001(2009).
[16] T.-Y. Chen, J. Wang, H. Liang, W.-Y. Liu, Y. Liu, X. Jiang, Y. Wang, X. Wan, W.-Q. Cai, L. Ju, L.-K. Chen, L.-J. Wang, Y. Gao, K. Chen, C.-Z. Peng, Z.-B. Chen, J.-W. Pan. Metropolitan all-pass and inter-city quantum communication network. Opt. Express, 18, 27217-27225(2010).
[17] M. Sasaki, M. Fujiwara, H. Ishizuka, W. Klaus, K. Wakui, M. Takeoka, S. Miki, T. Yamashita, Z. Wang, A. Tanaka, K. Yoshino, Y. Nambu, S. Takahashi, A. Tajima, A. Tomita, T. Domeki, T. Hasegawa, Y. Sakai, H. Kobayashi, T. Asai, K. Shimizu, T. Tokura, T. Tsurumaru, M. Matsui, T. Honjo, K. Tamaki, H. Takesue, Y. Tokura, J. F. Dynes, A. R. Dixon, A. W. Sharpe, Z. L. Yuan, A. J. Shields, S. Uchikoga, M. Legré, S. Robyr, P. Trinkler, L. Monat, J.-B. Page, G. Ribordy, A. Poppe, A. Allacher, O. Maurhart, T. Länger, M. Peev, A. Zeilinger. Field test of quantum key distribution in the Tokyo QKD network. Opt. Express, 19, 10387-10409(2011).
[18] Y.-A. Chen, Q. Zhang, T.-Y. Chen, W.-Q. Cai, S.-K. Liao, J. Zhang, K. Chen, J. Yin, J.-G. Ren, Z. Chen, S.-L. Han, Q. Yu, K. Liang, F. Zhou, X. Yuan, M.-S. Zhao, T.-Y. Wang, X. Jiang, L. Zhang, W.-Y. Liu, Y. Li, Q. Shen, Y. Cao, C.-Y. Lu, R. Shu, J.-Y. Wang, L. Li, N.-L. Liu, F. Xu, X.-B. Wang, C.-Z. Peng, J.-W. Pan. An integrated space-to-ground quantum communication network over 4,600 kilometres. Nature, 589, 214-219(2021).
[19] L. Lydersen, C. Wiechers, C. Wittmann, D. Elser, J. Skaar, V. Makarov. Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photonics, 4, 686-689(2010).
[20] I. Gerhardt, Q. Liu, A. Lamas-Linares, J. Skaar, C. Kurtsiefer, V. Makarov. Full-field implementation of a perfect eavesdropper on a quantum cryptography system. Nat. Commun., 2, 349(2011).
[21] H.-K. Lo, M. Curty, B. Qi. Measurement-device-independent quantum key distribution. Phys. Rev. Lett., 108, 130503(2012).
[22] S. L. Braunstein, S. Pirandola. Side-channel-free quantum key distribution. Phys. Rev. Lett., 108, 130502(2012).
[23] K. Tamaki, H.-K. Lo, C.-H. F. Fung, B. Qi. Phase encoding schemes for measurement-device-independent quantum key distribution with basis-dependent flaw. Phys. Rev. A, 85, 042307(2012).
[24] X.-B. Wang. Three-intensity decoy-state method for device-independent quantum key distribution with basis-dependent errors. Phys. Rev. A, 87, 012320(2013).
[25] M. Curty, F. Xu, W. Cui, C. C. W. Lim, K. Tamaki, H.-K. Lo. Finite-key analysis for measurement-device-independent quantum key distribution. Nat. Commun., 5, 3732(2014).
[26] F. Xu, M. Curty, B. Qi, H.-K. Lo. Practical aspects of measurement-device-independent quantum key distribution. New J. Phys., 15, 113007(2013).
[27] F. Xu, H. Xu, H.-K. Lo. Protocol choice and parameter optimization in decoy-state measurement-device-independent quantum key distribution. Phys. Rev. A, 89, 052333(2014).
[28] Z.-W. Yu, Y.-H. Zhou, X.-B. Wang. Statistical fluctuation analysis for measurement-device-independent quantum key distribution with three-intensity decoy-state method. Phys. Rev. A, 91, 032318(2015).
[29] Y.-H. Zhou, Z.-W. Yu, X.-B. Wang. Making the decoy-state measurement-device-independent quantum key distribution practically useful. Phys. Rev. A, 93, 042324(2016).
[30] H.-L. Yin, T.-Y. Chen, Z.-W. Yu, H. Liu, L.-X. You, Y.-H. Zhou, S.-J. Chen, Y. Mao, M.-Q. Huang, W.-J. Zhang, H. Chen, M. J. Li, D. Nolan, F. Zhou, X. Jiang, Z. Wang, Q. Zhang, X.-B. Wang, J.-W. Pan. Measurement-device-independent quantum key distribution over a 404 km optical fiber. Phys. Rev. Lett., 117, 190501(2016).
[31] Y. Cao, Y.-H. Li, K.-X. Yang, Y.-F. Jiang, S.-L. Li, X.-L. Hu, M. Abulizi, C.-L. Li, W. Zhang, Q.-C. Sun, W.-Y. Liu, X. Jiang, S.-K. Liao, J.-G. Ren, H. Li, L. You, Z. Wang, J. Yin, C.-Y. Lu, X.-B. Wang, Q. Zhang, C.-Z. Peng, J.-W. Pan. Long-distance free-space measurement-device-independent quantum key distribution. Phys. Rev. Lett., 125, 260503(2020).
[32] K. Wei, W. Li, H. Tan, Y. Li, H. Min, W.-J. Zhang, H. Li, L. You, Z. Wang, X. Jiang, T.-Y. Chen, S.-K. Liao, C.-Z. Peng, F. Xu, J.-W. Pan. High-speed measurement-device-independent quantum key distribution with integrated silicon photonics. Phys. Rev. X, 10, 031030(2020).
[33] H. Semenenko, P. Sibson, A. Hart, M. G. Thompson, J. G. Rarity, C. Erven. Chip-based measurement-device-independent quantum key distribution. Optica, 7, 238-242(2020).
[34] L. Cao, W. Luo, Y. Wang, J. Zou, R. D. Yan, H. Cai, Y. Zhang, X. L. Hu, C. Jiang, W. J. Fan, X. Q. Zhou, B. Dong, X. S. Luo, G. Q. Lo, Y. X. Wang, Z. W. Xu, S. H. Sun, X. B. Wang, Y. L. Hao, Y. F. Jin, D. L. Kwong, L. C. Kwek, A. Q. Liu. Chip-based measurement-device-independent quantum key distribution using integrated silicon photonic systems. Phys. Rev. Appl., 14, 011001(2020).
[35] L. Comandar, M. Lucamarini, B. Fröhlich, J. Dynes, A. Sharpe, S.-B. Tam, Z. Yuan, R. Penty, A. Shields. Quantum key distribution without detector vulnerabilities using optically seeded lasers. Nat. Photonics, 10, 312-315(2016).
[36] C. Wang, Z.-Q. Yin, S. Wang, W. Chen, G.-C. Guo, Z.-F. Han. Measurement-device-independent quantum key distribution robust against environmental disturbances. Optica, 4, 1016-1023(2017).
[37] G. Roberts, M. Lucamarini, Z. Yuan, J. Dynes, L. Comandar, A. Sharpe, A. Shields, M. Curty, I. Puthoor, E. Andersson. Experimental measurement-device-independent quantum digital signatures. Nat. Commun., 8, 1098(2017).
[38] C. Jiang, Z.-W. Yu, X.-L. Hu, X.-B. Wang. Higher key rate of measurement-device-independent quantum key distribution through joint data processing. Phys. Rev. A, 103, 012402(2021).
[39] Y.-P. Chen, J.-Y. Liu, M.-S. Sun, X.-X. Zhou, C.-H. Zhang, J. Li, Q. Wang. Experimental measurement-device-independent quantum key distribution with the double-scanning method. Opt. Lett., 46, 3729-3732(2021).
[40] M. Lucamarini, Z. L. Yuan, J. F. Dynes, A. J. Shields. Overcoming the rate–distance limit of quantum key distribution without quantum repeaters. Nature, 557, 400-403(2018).
[41] S. Pirandola, R. Laurenza, C. Ottaviani, L. Banchi. Fundamental limits of repeaterless quantum communications. Nat. Commun., 8, 15043(2017).
[42] X.-B. Wang, Z.-W. Yu, X.-L. Hu. Twin-field quantum key distribution with large misalignment error. Phys. Rev. A, 98, 062323(2018).
[43] K. Tamaki, H.-K. Lo, W. Wang, M. Lucamarini. Information theoretic security of quantum key distribution overcoming the repeaterless secret key capacity bound(2018).
[44] C. Cui, Z.-Q. Yin, R. Wang, W. Chen, S. Wang, G.-C. Guo, Z.-F. Han. Twin-field quantum key distribution without phase postselection. Phys. Rev. Appl., 11, 034053(2019).
[45] M. Curty, K. Azuma, H.-K. Lo. Simple security proof of twin-field type quantum key distribution protocol. npj Quantum Inf., 5, 64(2019).
[46] Z.-W. Yu, X.-L. Hu, C. Jiang, H. Xu, X.-B. Wang. Sending-or-not-sending twin-field quantum key distribution in practice. Sci. Rep., 9, 3080(2019).
[47] K. Maeda, T. Sasaki, M. Koashi. Repeaterless quantum key distribution with efficient finite-key analysis overcoming the rate-distance limit. Nat. Commun., 10, 3140(2019).
[48] C. Jiang, Z.-W. Yu, X.-L. Hu, X.-B. Wang. Unconditional security of sending or not sending twin-field quantum key distribution with finite pulses. Phys. Rev. Appl., 12, 024061(2019).
[49] H. Xu, Z.-W. Yu, C. Jiang, X.-L. Hu, X.-B. Wang. Sending-or-not-sending twin-field quantum key distribution: breaking the direct transmission key rate. Phys. Rev. A, 101, 042330(2020).
[50] G. Currás-Lorenzo, Á. Navarrete, K. Azuma, G. Kato, M. Curty, M. Razavi. Tight finite-key security for twin-field quantum key distribution. npj Quantum Inf., 7, 22(2021).
[51] C. Jiang, X.-L. Hu, Z.-W. Yu, X.-B. Wang. Composable security for practical quantum key distribution with two way classical communication. New J. Phys., 23, 063038(2021).
[52] M. Minder, M. Pittaluga, G. Roberts, M. Lucamarini, J. Dynes, Z. Yuan, A. Shields. Experimental quantum key distribution beyond the repeaterless secret key capacity. Nat. Photonics, 13, 334-338(2019).
[53] Y. Liu, Z.-W. Yu, W. Zhang, J.-Y. Guan, J.-P. Chen, C. Zhang, X.-L. Hu, H. Li, C. Jiang, J. Lin, T.-Y. Chen, L. You, Z. Wang, X.-B. Wang, Q. Zhang, J.-W. Pan. Experimental twin-field quantum key distribution through sending or not sending. Phys. Rev. Lett., 123, 100505(2019).
[54] S. Wang, D.-Y. He, Z.-Q. Yin, F.-Y. Lu, C.-H. Cui, W. Chen, Z. Zhou, G.-C. Guo, Z.-F. Han. Beating the fundamental rate-distance limit in a proof-of-principle quantum key distribution system. Phys. Rev. X, 9, 021046(2019).
[55] X. Zhong, J. Hu, M. Curty, L. Qian, H.-K. Lo. Proof-of-principle experimental demonstration of twin-field type quantum key distribution. Phys. Rev. Lett., 123, 100506(2019).
[56] J.-P. Chen, C. Zhang, Y. Liu, C. Jiang, W. Zhang, X.-L. Hu, J.-Y. Guan, Z.-W. Yu, H. Xu, J. Lin, M.-J. Li, H. Chen, H. Li, L. You, Z. Wang, X.-B. Wang, Q. Zhang, J.-W. Pan. Sending-or-not-sending with independent lasers: secure twin-field quantum key distribution over 509 km. Phys. Rev. Lett., 124, 070501(2020).
[57] X.-T. Fang, P. Zeng, H. Liu, M. Zou, W. Wu, Y.-L. Tang, Y.-J. Sheng, Y. Xiang, W. Zhang, H. Li, Z. Wang, L. You, M.-J. Li, H. Chen, Y.-A. Chen, Q. Zhang, C.-Z. Peng, X. Ma, T.-Y. Chen, J.-W. Pan. Implementation of quantum key distribution surpassing the linear rate-transmittance bound. Nat. Photonics, 14, 422-425(2020).
[58] H. Liu, C. Jiang, H.-T. Zhu, M. Zou, Z.-W. Yu, X.-L. Hu, H. Xu, S. Ma, Z. Han, J.-P. Chen, Y. Dai, S.-B. Tang, W. Zhang, H. Li, L. You, Z. Wang, Y. Hua, H. Hu, H. Zhang, F. Zhou, Q. Zhang, X.-B. Wang, T.-Y. Chen, J.-W. Pan. Field test of twin-field quantum key distribution through sending-or-not-sending over 428 km. Phys. Rev. Lett., 126, 250502(2021).
[59] J.-P. Chen, C. Zhang, Y. Liu, C. Jiang, W.-J. Zhang, Z.-Y. Han, S.-Z. Ma, X.-L. Hu, Y.-H. Li, H. Liu, F. Zhou, H.-F. Jiang, T.-Y. Chen, H. Li, L.-X. You, Z. Wang, X.-B. Wang, J.-W. Zhang, Q. Pan. Twin-field quantum key distribution over 511 km optical fiber linking two distant metropolitans. Nat. Photonics, 15, 570-575(2021).
[60] M. Pittaluga, M. Minder, M. Lucamarini, M. Sanzaro, R. I. Woodward, M.-J. Li, Z. Yuan, A. J. Shields. 600 km repeater-like quantum communications with dual-band stabilization. Nat. Photonics, 15, 530-535(2021).
[61] H. Chernoff. A measure of asymptotic efficiency for tests of a hypothesis based on the sum of observations. Ann. Math. Stat., 23, 493-507(1952).
[62] X.-L. Hu, Z.-W. Yu, X.-B. Wang. Efficient measurement-device-independent quantum key distribution without vacuum sources. Phys. Rev. A, 98, 032303(2018).
[63] Z. Yuan, A. Plews, R. Takahashi, K. Doi, W. Tam, A. W. Sharpe, A. R. Dixon, E. Lavelle, J. F. Dynes, A. Murakami, M. Kujiraoka, M. Lucamarini, Y. Tanizawa, H. Sato, A. J. Shields. 10-Mb/s quantum key distribution. J. Lightwave Technol., 36, 3427-3433(2018).
Set citation alerts for the article
Please enter your email address



