[1] Wang D, Cheng H B, He D B et al. On the challenges in designing identity-based privacy-preserving authentication schemes for mobile devices[J]. IEEE Systems Journal, 12, 916-925(2018).
[2] Meng Y X, Wong D S, Schlegel R et al. Touch gestures based biometric authentication scheme for touchscreen mobile phones[M]. ∥Kutyłowski M, Yung M. Information security and cryptology. Lecture notes in computer science. Berlin, Heidelberg: Springer, 7763, 331-350(2013).
[3] Ganesh S M, Vijayakumar P, Deborah L J. A secure gesture based authentication scheme to unlock the smartphones. [C]∥2017 Second International Conference on Recent Trends and Challenges in Computational Models (ICRTCCM), February 3-4, 2017, Tindivanam, Tamilnadu, India. New York: IEEE, 153-158(2017).
[4] Liu Y[J]. Study on the cost risk evaluation model of power transmission project based on bill-of-quantity model Automation & Instrumentation, 2018, 23-26.
[5] Song C, Zhang Y D, Wang L et al. Trajectory privacy protection scheme based on DTW exchange query[J]. Journal of Beijing University of Posts and Telecommunications, 41, 97-102(2018).
[6] Miao Y Q, Wang L N, Xie C Y et al. Gesture recognition based on deep belief networks[M]. ∥Zhou J, Wang Y H, Sun Z N, et al. Gesture recognition based on deep belief networks. Lecture notes in computer science. Cham: Springer, 10568, 439-446(2017).
[7] Ma Y X, Hao Y X, Chen M et al. Audio-visual emotion fusion (AVEF): a deep efficient weighted approach[J]. Information Fusion, 46, 184-192(2019).
[8] Lee H, Grosse R, Ranganath R et al. Convolutional deep belief networks for scalable unsupervised learning of hierarchical representations. [C]∥Proceedings of the 26th Annual International Conference on Machine Learning-ICML'09, June 14-18, 2009, Montreal, Quebec, Canada. New York: ACM, 609-616(2009).
[9] Bell S, Zitnick C L, Bala K et al. Inside-outside net: detecting objects in context with skip pooling and recurrent neural networks. [C]∥2016 IEEE Conference on Computer Vision and Pattern Recognition (CVPR), June 27-30, 2016, Las Vegas, NV, USA. New York: IEEE, 2874-2883(2016).
[11] Zhao R, Yan R Q, Chen Z H et al. Deep learning and its applications to machine health monitoring[J]. Mechanical Systems and Signal Processing, 115, 213-237(2019).
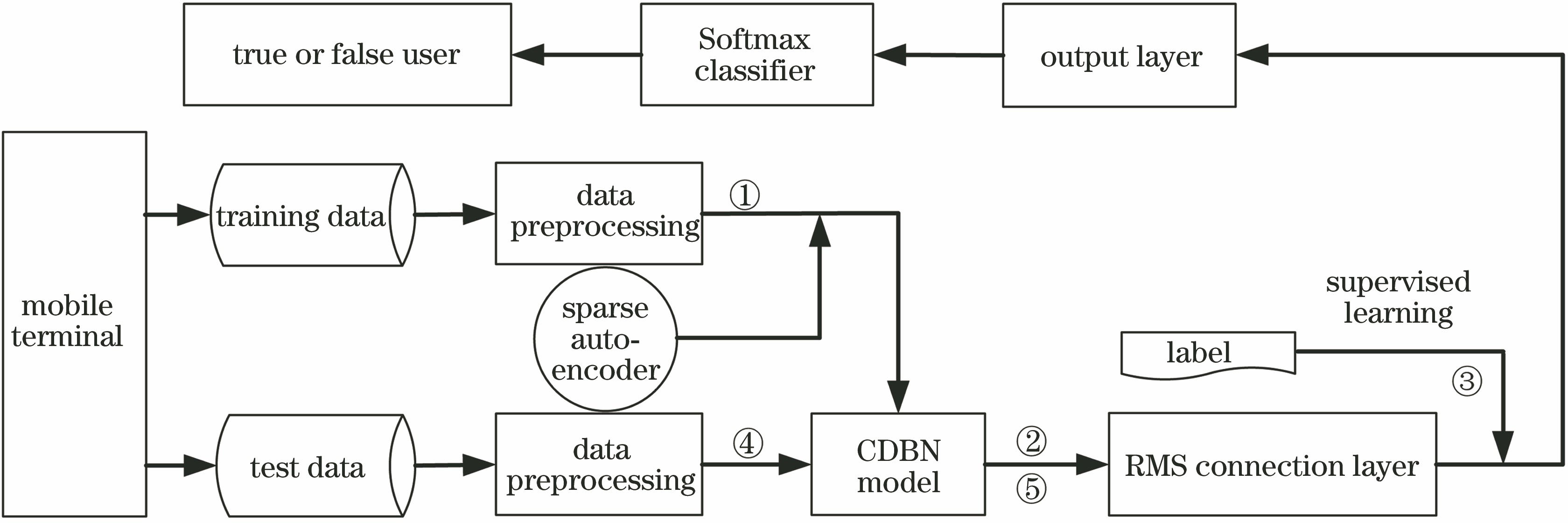
[12] Sun Z W, Zhang Y C[J]. Deep belief network model for mobile terminal identity authentication Netinfo Security, 2019, 34-42.
[13] Rzecki K, Pławiak P et al. Nied
[15] Khaw M W, Glimcher P W, Louie K. Normalized value coding explains dynamic adaptation in the human valuation process[J]. Proceedings of the National Academy of Sciences, 114, 12696-12701(2017).
[16] Lee H, Pham P, Largman Y et al. Unsupervised feature learning for audio classification using convolutional deep belief networks. [C]∥Advances in Neural Information Processing Systems, December 7-10, 2009, Vancouver, British Columbia, Canada. Canada: NIPS, 1096-1104(2009).
[17] Norouzi M. Convolutional restricted Boltzmann machines for feature learning[D]. Vancouver: Simon Fraser University(2009).
[18] He Z B. Singer identification using convolutional deep belief networks[D]. Guangzhou: South China University of Technology(2015).
[19] Norouzi M, Ranjbar M, Mori G. Stacks of convolutional restricted Boltzmann machines for shift-invariant feature learning. [C]∥2009 IEEE Conference on Computer Vision and Pattern Recognition, June 20-25, 2009, Miami, FL, USA. New York: IEEE, 2735-2742(2009).