[2] A. K. Ekert. Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett., 67, 661(1991).
[3] D. P. DiVincenzo. Quantum computation. Science, 270, 255(1995).
[4] R. Horodecki, P. Horodecki, M. Horodecki. Quantum entanglement. Rev. Mod. Phys., 81, 865(2009).
[6] D. F. V. James, P. G. Kwiat, W. J. Munro. Measurement of qubits. Phys. Rev. A, 64, 052312(2001).
[8] R. Hildebrand. Concurrence revisited. J. Math. Phys., 48, 102108(2007).
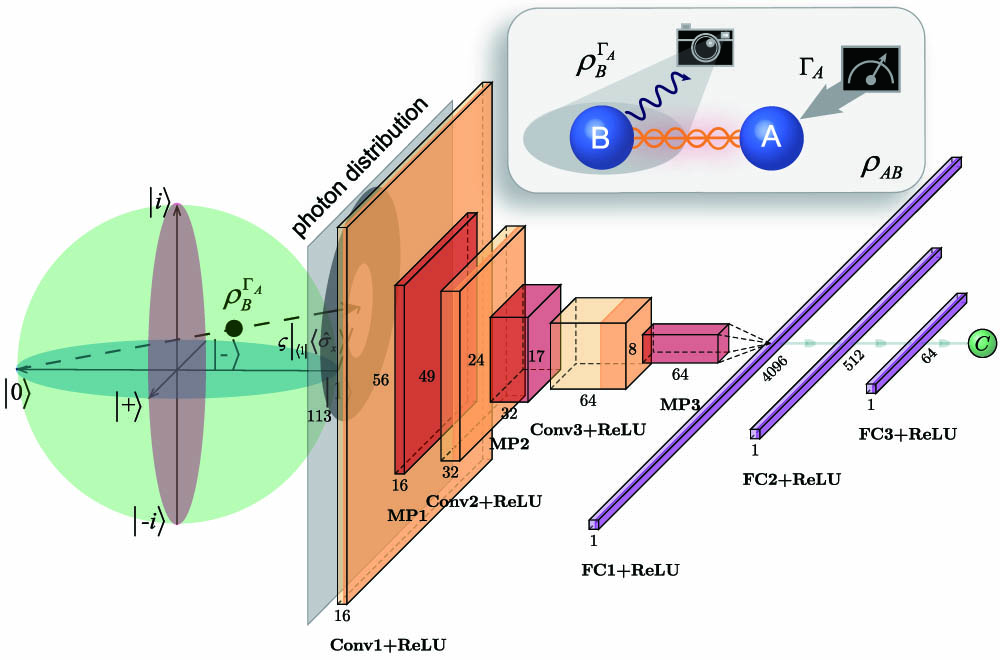
[16] K. O’Shea, R. Nash. An introduction to convolutional neural networks. arXiv(2015).
[22] Y. LeCun, Y. Bengio, G. Hinton. Deep learning. Nature, 521, 436-444(2015).
[27] D. P. Kingma, J. Ba. Adam: a method for stochastic optimization. arXiv(2014).