[1] Deng D P, Li H S, Lin C S et al[J]. Study on a new fiber-optic cable tapping and detection technology Study on Optical Communications, 2007, 55-58.
[2] Chen H, Zhu S X. Exploration on optical fiber wiretapping and intrusion detection[J]. China Information Security, 10, 61-63(2012).
[3] Shor P W. Polynomial-time algorithms for prime factorization and discrete logarithms on a quantum computer[J]. SIAM Review, 41, 303-332(1999).
[4] Grover L K. A fast quantum mechanical algorithm for database search[C]∥Proceedings of the Twenty-Eighth Annual ACM Symposium on Theory of Computing-STOC '96, May 22-24, 1996, Philadelphia, Pennsylvania, USA. New , 212-219(1996).
[7] Lo H. Unconditional security of quantum key distribution over arbitrarily long distances[J]. Science, 283, 2050-2056(1999).
[8] Scarani V, Bechmann-Pasquinucci H, Cerf N J et al. The security of practical quantum key distribution[J]. Reviews of Modern Physics, 81, 1301-1350(2009).
[9] Patel K A, Dynes J F, Lucamarini M et al. Quantum key distribution for 10 Gb/s dense wavelength division multiplexing networks[J]. Applied Physics Letters, 104, 051123(2014).
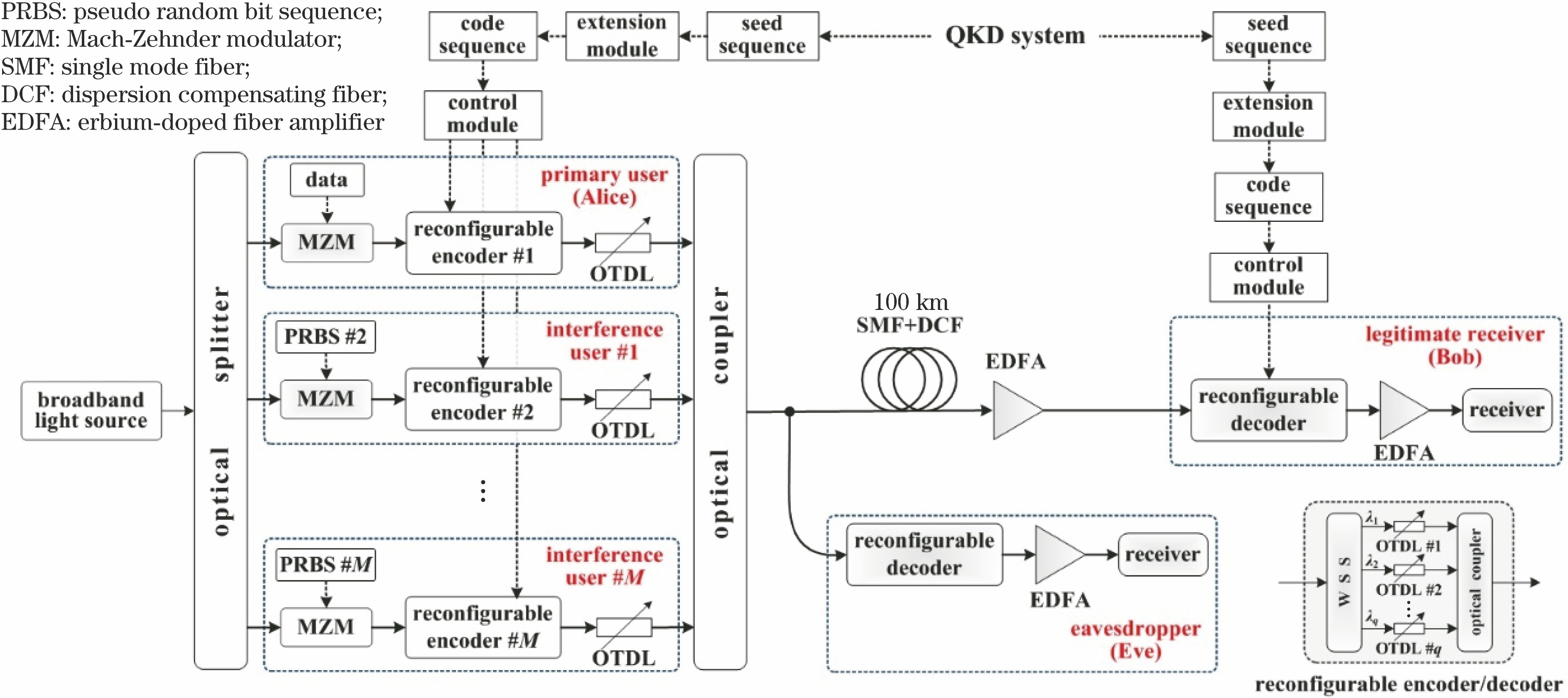
[10] Shake T H. Security performance of optical CDMAA gainst eavesdropping[J]. Journal of Lightwave Technology, 23, 655-670(2005).
[11] Leaird D E, Huang C B, Jiang Z et al. DPSK based eavesdropper vulnerability in two-code keyed O-CDMA systems. [C]∥2008 Conference on Optical Fiber Communication/National Fiber Optic Engineers Conference, February 24-28, 2008, San Diego, CA, USA. New York: IEEE, OTuP2(2008).
[12] Wang Z X, Chang J, Prucnal P R. Theoretic alanalysis and experimental investigation on the confidentiality of 2-D incoherent optical CDMA system[J]. Journal of Lightwave Technology, 28, 1761-1769(2010).
[13] Ji J H, Zhang G R, Li W J et al. Performance analysis of physical-layer security in an OCDMA-based wiretap channel[J]. Journal of Optical Communications and Networking, 9, 813-818(2017).
[14] Ji J H, Huang Q, Chen X M et al. Performance analysis and experimental investigation of physical-layer security in OCDMA-based hybrid FSO/fiber wiretap channel[J]. IEEE Photonics Journal, 11, 1-20(2019).
[15] Gupta S, Goel A. Advance method for security enhancement in optical code Division multiple access system[J]. IETE Journal of Research, 64, 17-26(2018).
[16] Tsujioka T. Hara S. A code reconfiguration design for two dimensional OCDMA system to enhance security. [C]∥2007 IFIP International Conference on Wireless and Optical Communications Networks, July 2-4, 2007, Singapore. IEEE, 9793863(2007).
[17] Singh S, Kaur R, Singh A et al. Novel security enhancement technique against eavesdropper for OCDMA system using 2-D modulation format with code switching scheme[J]. Optical Fiber Technology, 22, 84-89(2015).
[18] Jyoti V, Kaler R S. Security enhancement of OCDMA system against eavesdropping using code-switching scheme[J]. Optik, 122, 787-791(2011).