[1] Ozturk C, Zhang Y Y, Trappe W. Source-location privacy in energy-constrained sensor network routing. [C]∥Proceedings of the 2nd ACM workshop on Security of ad hoc and sensor networks-SASN'04, October 25, 2004. Washington DC, USA. New York: ACM, 88-93(2004).
[2] Kamat P, Zhang Y, Trappe W et al. Enhancing source-location privacy in sensor network routing. [C]∥25th IEEE International Conference on Distributed Computing Systems (ICDCS'05), June 6-10, 2005, Columbus, OH, USA. New York: IEEE, 599-608(2005).
[3] Li X F, Mao Y C, Liang Y. A survey on topology control in wireless sensor networks. [C]∥2008 10th International Conference on Control, Automation, Robotics and Vision, December 17-20, 2008, Hanoi, Vietnam. New York: IEEE, 251-255(2008).
[5] Li Y, Lightfoot L, Ren J. Routing-based source-location privacy protection in wireless sensor networks. [C]∥2009 IEEE International Conference on Electro/Information Technology, June 7-9, 2009, Windsor, ON, Canada. New York: IEEE, 29-34(2009).
[6] Lopez J, Rios R, Cuellar J. Preserving receiver-location privacy in wireless sensor networks[M]. ∥Huang X, Zhou J. Information security practice and experience. Lecture notes in computer science. Cham: Springer, 15-27(2014).
[11] Chun C L. Research on source location privacy protection in wireless sensor networks[D]. Tianjin: Tianjin University(2016).
[12] Yuan S Q. Research on source location privacy protection in wireless sensor networks[D]. Tianjin: Tianjin University(2017).
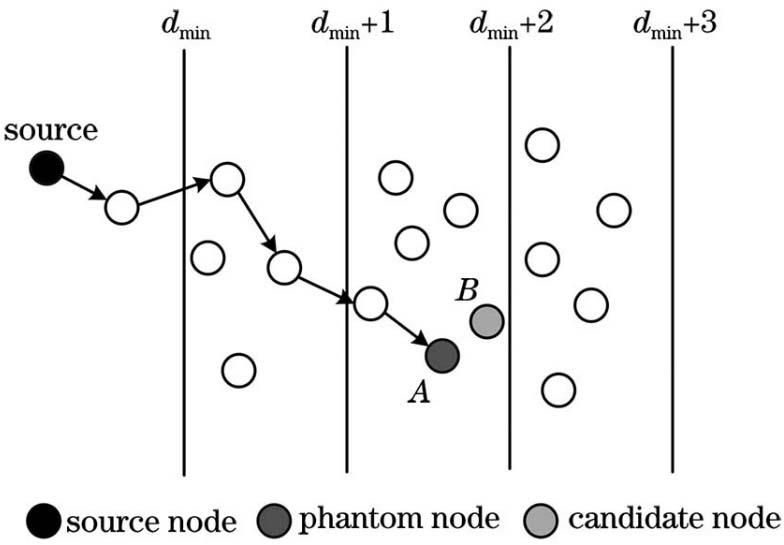
[13] Zhou C, Hu X H. Phantom routing privacy protocol based on directed random in WSN[J]. Application Research of Computers, 35, 3109-3112(2018).
[14] Ni G Y. Research of node privacy protection in IoT perception layer[D]. Nanjing: Southeast University(2016).
[15] Zhang J N, Chu C L. A scheme to protect the source location privacy in wireless sensor networks[J]. Chinese Journal of Sensors and Actuators, 29, 1405-1409(2016).
[16] Zhang L. Research of location privacy protection in IoT perception layer[D]. Nanjing: Southeast University(2015).