Jing Wang, Yuchen Zhang, Zhanqiang Huo, Liqin Jia. Image Tampering Detection Method Based on Approximate Nearest Neighbor Search[J]. Laser & Optoelectronics Progress, 2020, 57(10): 101102
Search by keywords or author
- Laser & Optoelectronics Progress
- Vol. 57, Issue 10, 101102 (2020)
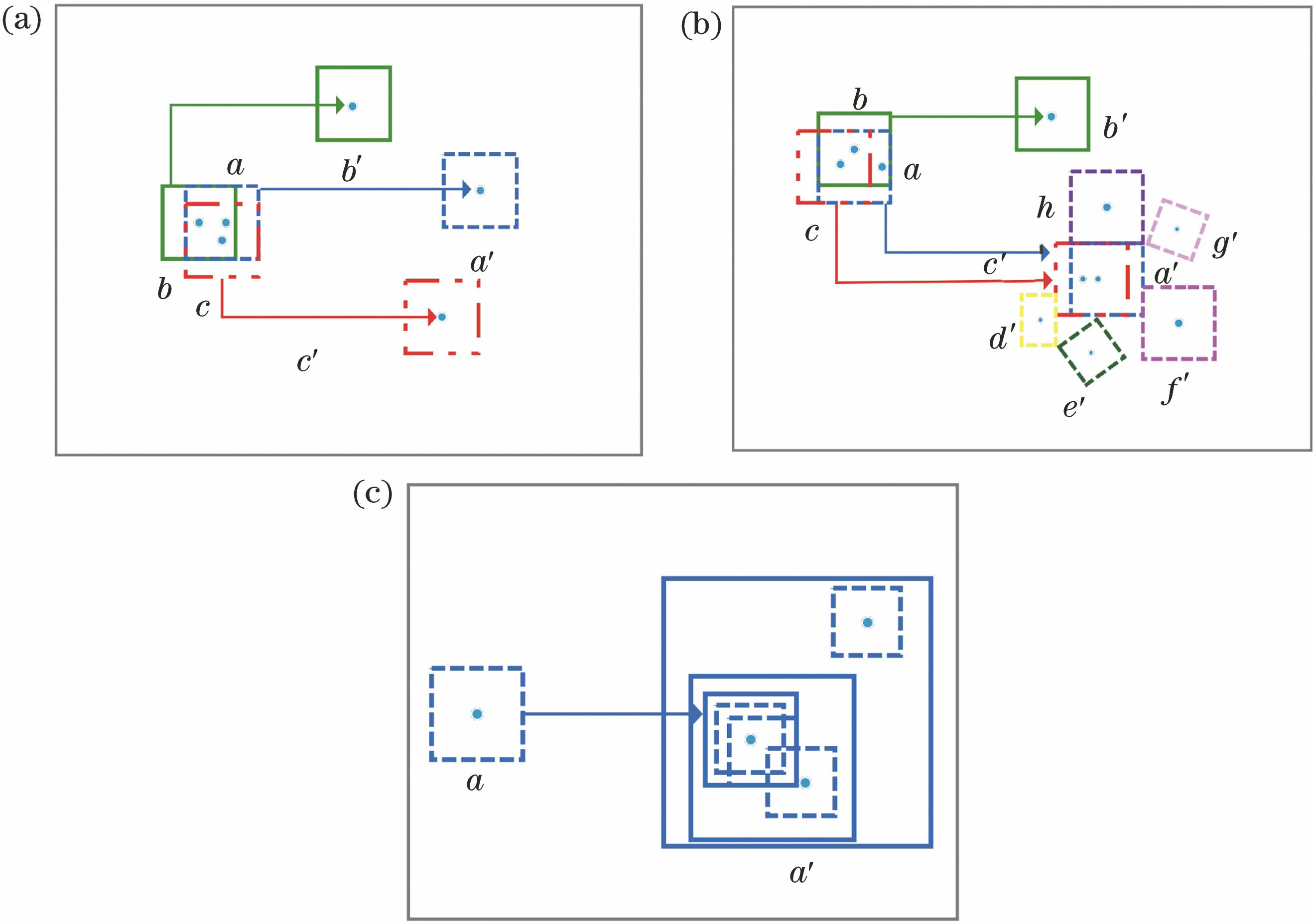
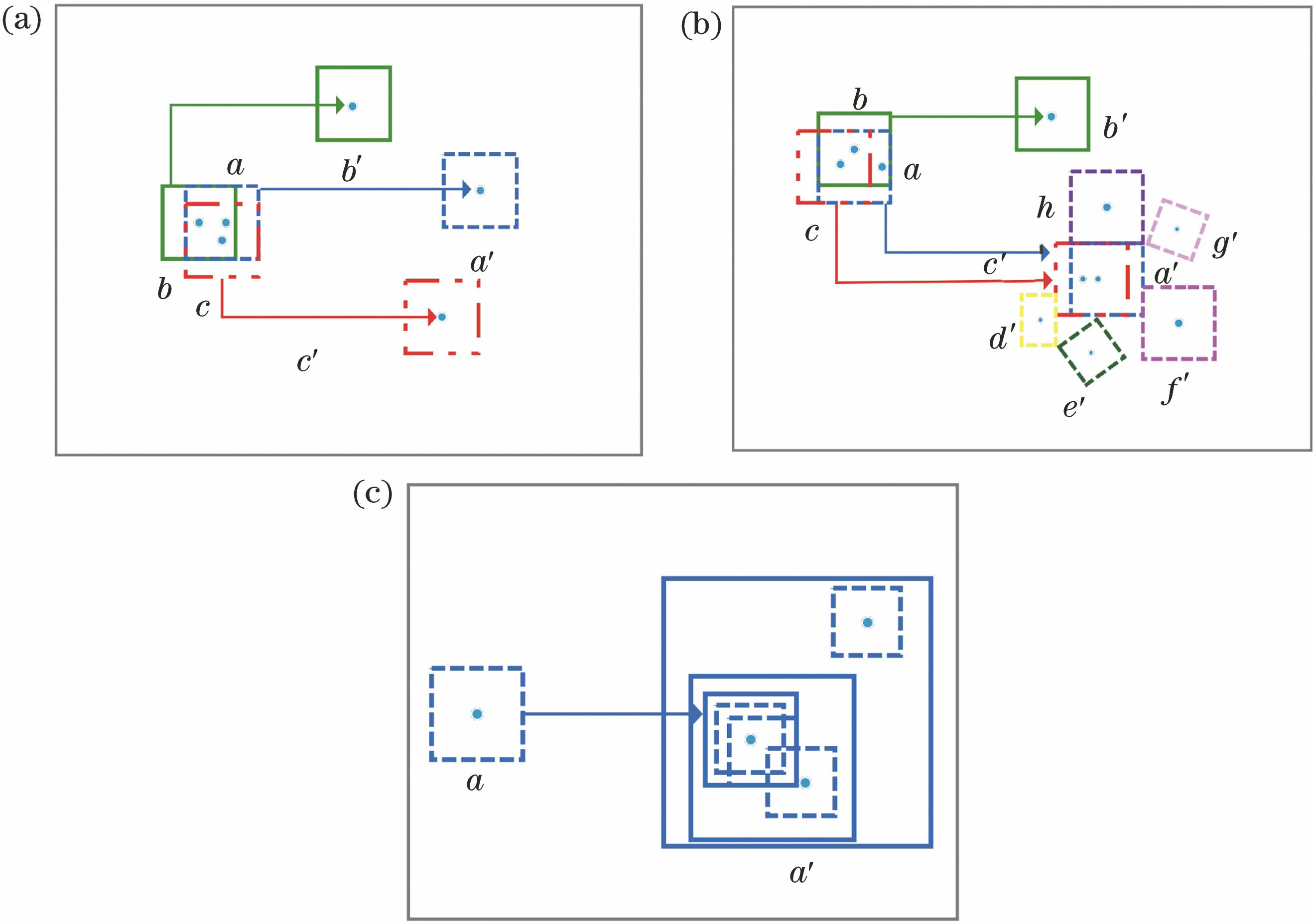
Fig. 1. Feature matching steps. (a) Initialization; (b) propagation; (c) random search
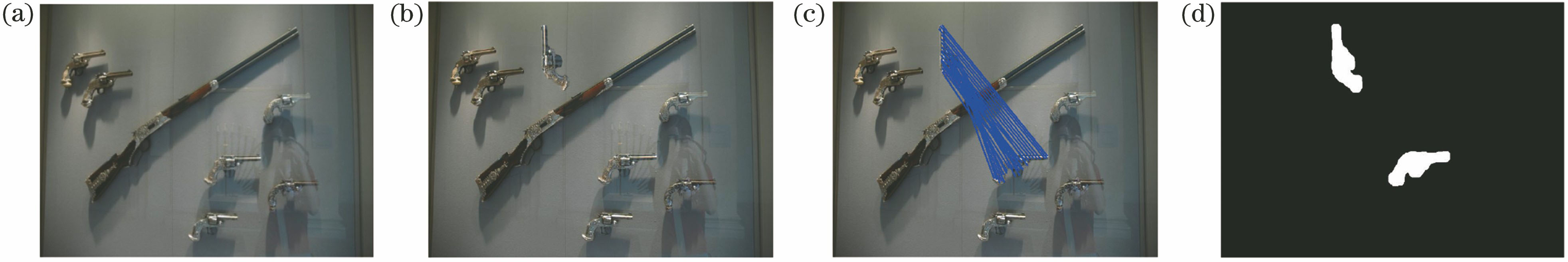
Fig. 2. Detection results of the algorithm on rotation transform operation. (a) Original image; (b) tampering image (rotation 90°); (c) matching result; (d) detection result
Fig. 3. Detection results of the algorithm on scaling transformation operation. (a) Original image; (b) tampering image (reduced by 80%); (c) matching result; (d) detection result
Fig. 4. Detection results of the algorithm on mirror transformation operation. (a) Original image; (b) mirror image (horizontal); (c) matching result; (d) detection result
Fig. 5. Detection results of the algorithm for multi-region I transform operation. (a) Original image; (b) tampering image; (c) matching result; (d) detection result
Fig. 6. Detection results of the algorithm for multi-region II transform operation. (a) Original image; (b) tampering image; (c) matching result; (d) detection result
Fig. 7. Detection results of the algorithm for multi-region mirroring I transform operation. (a) Original image; (b) tampering image; (c) matching result; (d) detection result
Fig. 8. Detection results of the algorithm for multi-region mirroring II transform operation. (a) Original image; (b) tampering image; (c) matching result; (d) detection result
|
Table 1. Experimental parameters
|
Table 2. F-measure of algorithm detection under different tampering operations%
|
Table 3. Comparison of average running time of different algorithmss
| |||||||||||||||||||||||
Table 4. Comparison of tampering detection performance of different algorithms under mirror operation
Set citation alerts for the article
Please enter your email address



