Yi Qin, Tianlong Man, Yuhong Wan, Xing Wang. Advances in Optical Image Compression and Encryption Methods[J]. Laser & Optoelectronics Progress, 2023, 60(4): 0400001
Search by keywords or author
- Laser & Optoelectronics Progress
- Vol. 60, Issue 4, 0400001 (2023)
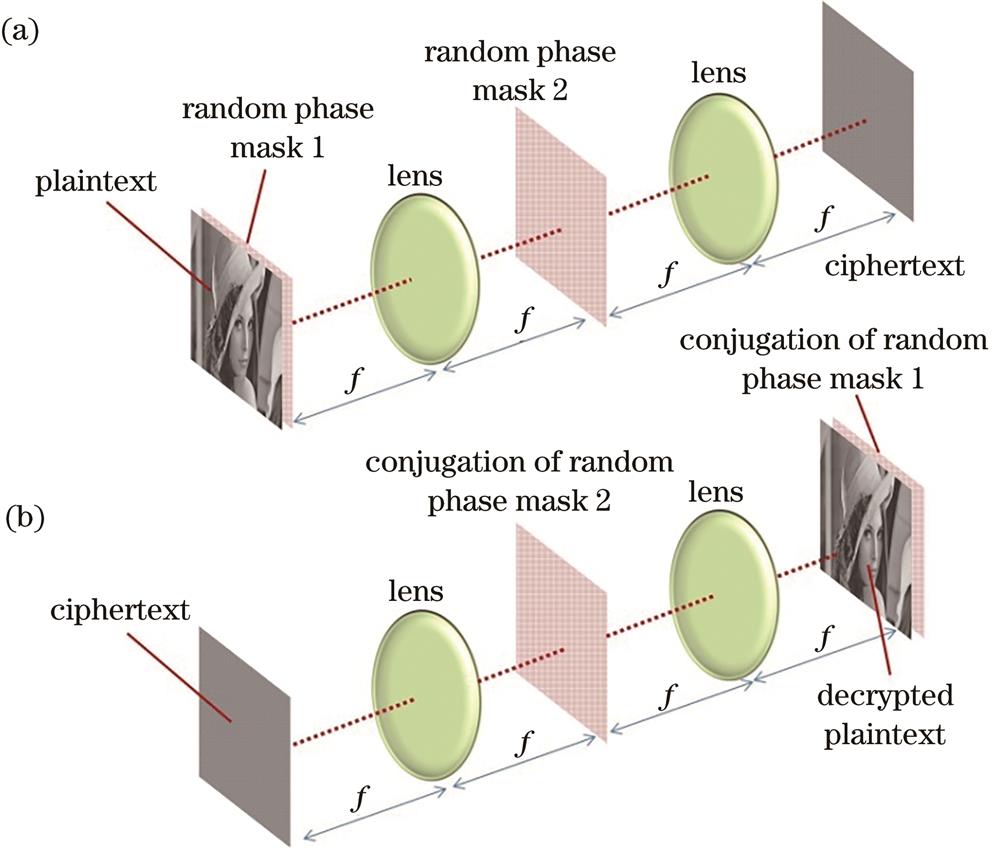
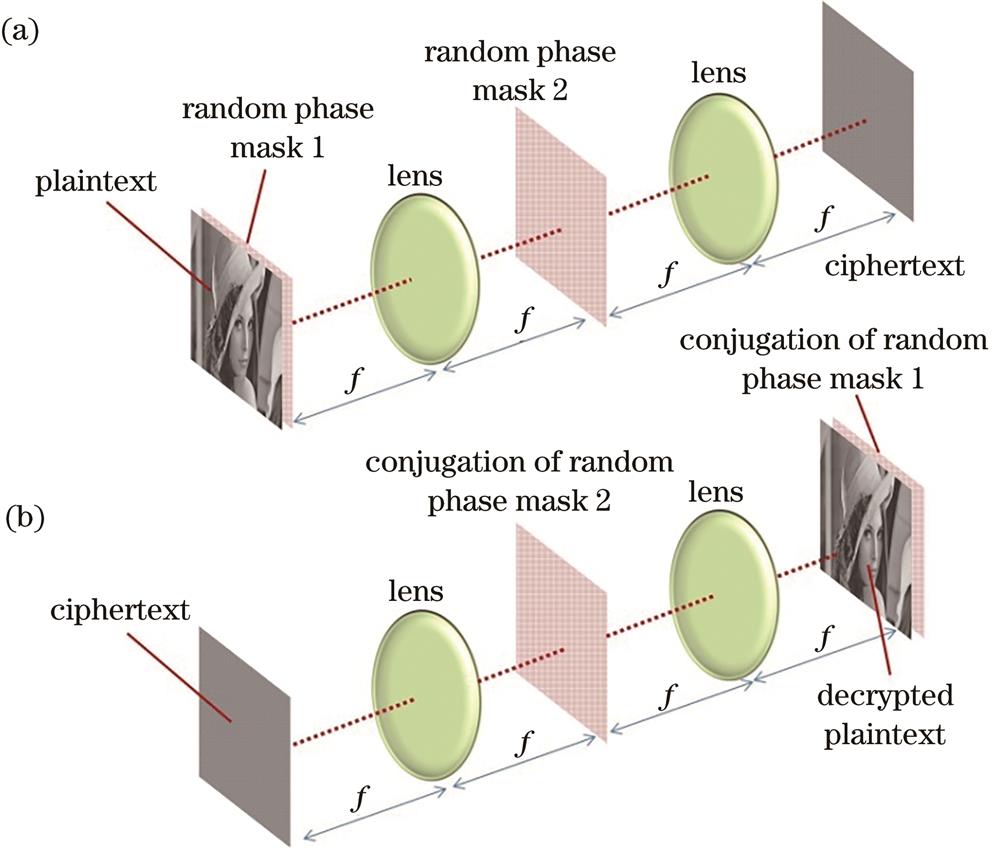
Fig. 1. Optical implementation of double random phase encoding. (a) Encryption; (b) decryption
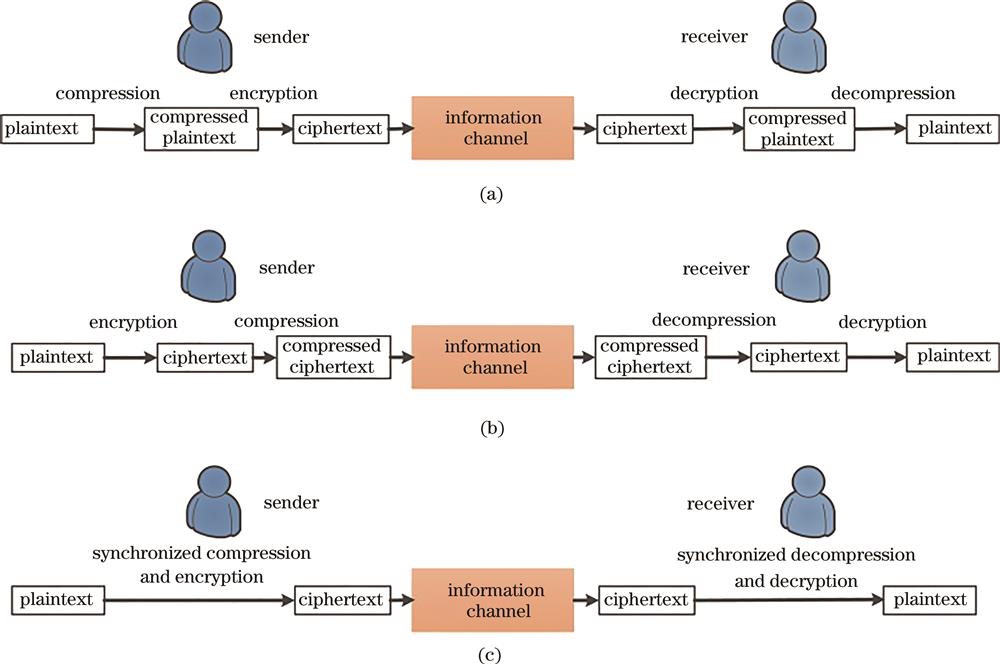
Fig. 2. Information processing flowchart for different compression strategies in optical compression-encryption system. (a) Plaintext compression; (b) ciphertext compression; (c) synchronized compression
Fig. 3. An example of information compression by using the concentration of energy in the transform domain
Fig. 4. Principle of G-S algorithm
Fig. 5. Single pixel camera based on compressive sensing[41]
Fig. 6. Double-image encryption based on frequency spectral fusion[44]
Fig. 7. Simulation results of multiple-image encryption based on frequency spectral fusion[44]. (a) Original images; (b) ciphertext; (c) decrypted images
Fig. 8. Multiple-image compression and encryption based on Radon transform[52]
Fig. 9. Image encryption and decryption process based on compression sensing and dual random phase coding system[55]
Fig. 10. Simulation results of image encryption system based on compression sensing and double random phase coding[55]. (a) Original image; (b) image downsampled by sensing matrix; (c) host image; (d) ciphertext; (e) combined image containing cipher information; (f) reconstructed image
Fig. 11. Schematic of optical encryption process based on spatial multiplexing and compression sensing[58]
Fig. 12. Schematic of optical decryption process based on spatial multiplexing and compression sensing[58]
Fig. 13. Multiple-image encryption based on position multiplexing[63]. (a) Encryption; (b) decryption
Fig. 14. Numerical simulation results of multiple-image encryption scheme based on position multiplexing [63]. (a) Ciphertext; (b) decryption corresponding to position
Fig. 15. Theta-modulation-based multiple-image encryption[71]
Fig. 16. Reconstruction of ciphertexts in theta-modulation-based multiple-image encryption[71]
Fig. 17. Reconstruction of plaintexts in theta-modulation-based multiple-image encryption[71]
Fig. 18. Multiple-image encryption based on angular multiplexing of CCD[75]
Fig. 19. Spectrum of the synthetic ciphertextofmultiple-image encryption based on angular multiplexing of CCD[75]. (a) Simulation result; (b) experimental result
Fig. 20. Decrypted results obtained by quantizing each pixel value in the ciphertext by different orders[30]. (a) 4 bits; (b) 3 bits; (c) 2 bits
Fig. 21. Optical ciphertext compression method based on deep learning[82]. (a) Compression; (b) decompression
Fig. 22. Comparison of the deep-learning-based optical ciphertext compression approach with JPEG and JPEG2000[82]
Fig. 23. Optical encryption based on compressive ghost imaging encryption[29]
Fig. 24. Decrypted results using compressive ghost imaging[29]. (a) Plaintext; (b) decrypted result obtained by conventional method under 3500 samplings; (c) decrypted result obtained by compressive sensing under 3500 samplings; (d) decrypted result obtained by compressive sensing under 200 samplings
Fig. 25. Encryption system based on single pixel imaging, phase shifting holography, and random phase coding[90]
Fig. 26. Decryption result of gray image obtained by encryption system[90]. (a) Plaintext; (b) one of the encrypted holograms on the DMD plane; (c) retrieved image of about 256×256×42.1% measurements, where 256×256 denotes the pixel count and 42.1% denotes the sampling ratio
Fig. 27. Optical decryption scheme of multi-image encryption system based on multi-plane phase recovery and interference principle[93]
Fig. 28. Iterative algorithm of multi-image encryption system based on multi-plane phase recovery algorithm and interference principle[93]
Fig. 29. Multiple-image encryption based on 3D space and phase retrieval algorithm[94]
Fig. 30. Multiple-image encryption based on azimuth multiplexing and phase retrieval algorithm[95]
Fig. 31. Iterative cryptosystem based on amplitude constraint in input plane[97]. (a) Decryption optical path and iterative algorithm basis; (b) amplitude constraint in input plane; (c) amplitude constraint in output plane
Fig. 32. Ciphertext combination method based on spatial multiplexing[97]
Fig. 34. Secret sharing (multiple-image encryption) system based on metasurface and iterative algorithm[33]
Fig. 35. Optical diffractive-imaging-based encryption scheme
Fig. 36. Effect of decryption algorithm of single exposure optical diffraction imaging encryption system[107]. (a) Decrypted image; (b) dependence of CC on iteration number; (c) dependence of CC on iteration number corresponding to the first iterative procedure; (d) dependence of CC on iteration number corresponding to the second iterative procedure
Fig. 37. Multi-image encryption system based on multimode phase retrieval algorithm and focal length multiplexing[110]
Fig. 38. Relationship between the quality of the decrypted images (CC) and the iteration number in the multi-image encryption system based on multimode phase retrieval algorithm and focal length multiplexing[110]
Fig. 39. Single exposure color image encryption system based on multimodal diffraction imaging[111]
Fig. 40. Multiple-image encryption based on compressive holography[114]
Fig. 41. Decrypted results of multiple-image encryption based on compressive holography[114]. (a)-(c) Plaintexts; (d) one of the holograms; (e)-(g) decrypted results
|
Table 1. Compression strategies and methods for optical image compression-encryption
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Table 2. Results by applying several classical compression methods to the original ciphertext[30]
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Table 3. Results by applying several classical compression methods to the quantized ciphertext[30]
|
Table 4. Comparison and analysis of the aforementioned compression methods
Set citation alerts for the article
Please enter your email address



