[1] Bennett C, Brassard G. Quantum cryptography:public key distribution and coin tossing[J]. Theoretical Computer Science, 560, 7-11(2014).
[2] Ekert A K. Quantum cryptography based on Bell’s theorem[J]. Physical Review Letters, 67, 661-663(1991).
[3] Gong F, Yang X, Wang T Y. Improvement of self-referenced continuous variable quantum key distribution using optical amplifier[J]. Laser&Optoelectronics Progress, 56, 212702(2019).
[4] Huang B, Huang Y M, Peng Z M. Attack and detection on reference-pulse phase of continuous-variable quantum-key distribution[J]. Acta Optica Sinica, 39, 1127001(2019).
[5] Ma S T, Guo D B, Xue Z et al. Multidimensional reconciliation for continuous-variable quantum key distribution based on two-edge type low-density parity-check codes[J]. Acta Optica Sinica, 39, 0527001(2019).
[6] Grosshans F, Grangier P. Continuous variable quantum cryptography using coherent states[J]. Physical Review Letters, 88, 057902(2002).
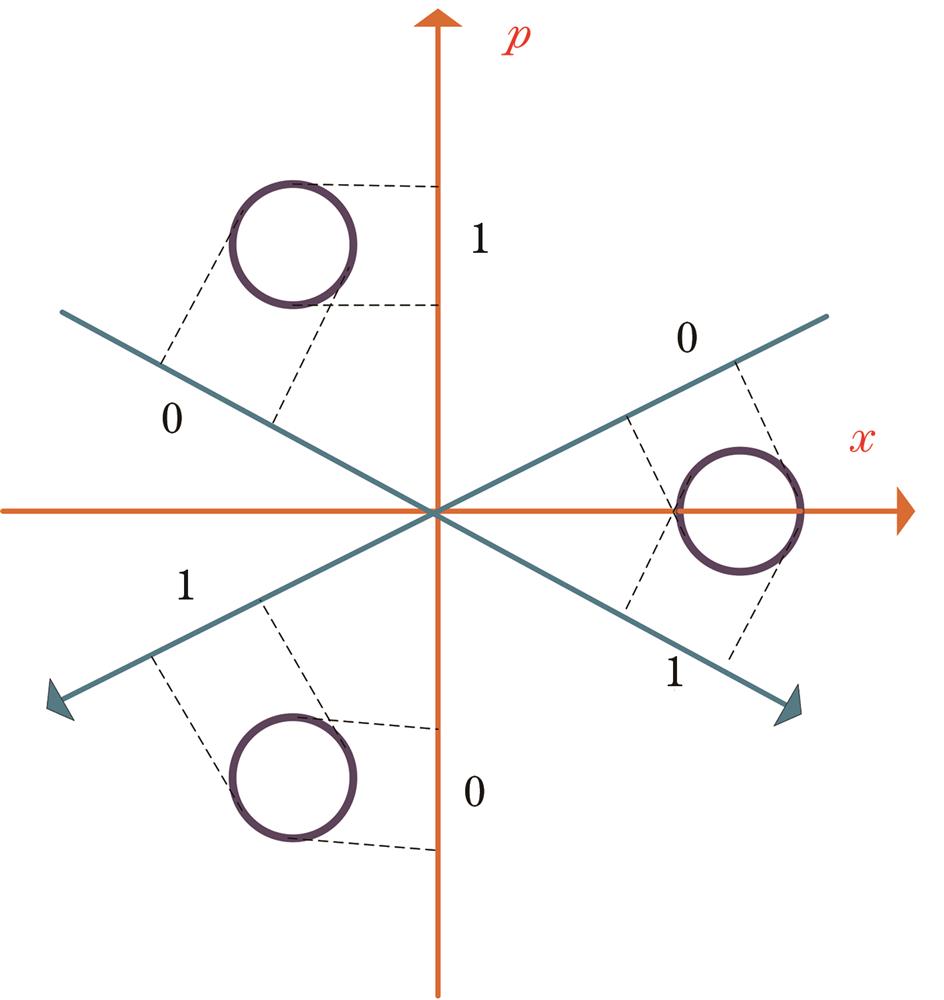
[7] Shen Y, Zou H, Tian L et al. Experimental study on discretely modulated continuous-variable quantum key distribution[J]. Physical Review A, 82, 022317(2012).
[8] Grosshans F, Cer N J, Wenger J et al. Virtual entanglement and reconciliation protocols for quantum cryptography with continuous variables[J]. Quantum Information and Computation, 3, 535-552(2003).
[9] Garcia-Patron R, Cerf N J. Unconditional optimality of Gaussian attacks against continuous variable quantum key distribution[J]. Physical Review Letters, 97, 190503(2006).
[10] Navascues M, Grosshans F, Acin A. Optimality of Gaussian attacks in continuous-variable quantum cryptography[J]. Physical Review Letters, 97, 190502(2006).
[11] Hirano T, Ichikawa T, Matsubara T et al. Implementation of continuous-variable quantum key distribution with discrete modulation[J]. Quantum Science and Technology, 2, 024010(2017).
[12] Bradler K, Weedbrook C. A security proof of continuous-variable QKD using three coherent states[J]. Physical Review A, 97, 022310(2017).
[13] Grosshans F, Assche G V, Wenger J et al. Quantum key distribution using gaussian-modulated coherent states[J]. Nature, 421, 238-241(2003).
[14] Namiki R and Hirano T. Efficient-phase-encoding protocols for continuous-variable quantum key distribution using coherent states and postselection[J]. Physical Review A, 74, 032302(2006).
[15] Symul T, Alto D J, Assad S M et al. Experimental demonstration of post-selection-based continuous-variable quantum key distribution in the presence of Gaussian noise[J]. Physical Review A, 76, 030303(2007).
[16] Heid M. Security of coherent state quantum cryptography in the presence of Gaussian noise[J]. Physical Review A, 76, 022313(2009).
[17] Holevo A S. Bounds for the quantity of information transmittable by a quantum communications channel[J]. Problems of Information Transmission, 9, 177-183(1973).
[18] Panagiotis P, Cosmo L, Christian W et al. Quantum key distribution with phase-encoded coherent states: asymptotic security analysis in thermal-loss channels[J]. Physical Review A, 98, 012340(2018).
[19] Leverrier A, Grangier P. Erratum: unconditional security proof of long-distance continuous-variable quantum key distribution with discrete modulation[J]. Physical Review Letters, 106, 259902(2009).