[1] Wu L F, Ma Y K, Zhou P et al. Review of biometric template protection[J]. Chinese Journal of Scientific Instrument, 37, 2407-2420(2016).
[2] Wang H Y, Tang S J, Ding Y et al. Survey on biometrics template protection[J]. Journal of Computer Research and Development, 57, 1003-1021(2020).
[4] Wang H S, Zhang X F. Improved BioHashing fingerprint template protection algorithms[J]. Acta Automatica Sinica, 44, 760-768(2018).
[5] Xu Q W, Zhang X F. Improved BioHashing fingerprint template protection algorithm[J]. Computer Applications and Software, 34, 256-261, 303(2017).
[8] Ding Y, Li J H, Tang S J et al. Template protection of speaker recognition based on random mapping technology[J]. Journal of Computer Research and Development, 57, 2201-2208(2020).
[10] Huang L Q, Liu H, Wang Z Y et al. Self-adaptive image encryption algorithm combining chaotic map with DNA computing[J]. Journal of Chinese Computer Systems, 41, 1959-1965(2020).
[13] Yuan L, Li W M. Face and ear fusion template protection based on fuzzy vaults[J]. Chinese Journal of Engineering, 37, 1225-1229(2015).
[17] Li Y N, Zhang X F. Cancelable palmprint template method based on secure sketch[J]. Computer Engineering and Applications, 54, 115-120(2018).
[18] Li Y N, Zhang X F. Generation algorithm of revocable palmprint template based on safety profile[J]. Computer Engineering and Applications, 54, 115-120(2018).
[19] Yang X H, Liu H X, Xiao J L. Extraction and relevance evaluation for multimodal biometric features[J]. Journal of Image and Graphics, 25, 1529-1538(2020).
[20] Peng J L. Research on key issues of multi-modal biometric verification based on finger[D](2014).
[21] Yuan L, Li W M, Mu Z C. Face and ear multimodal biometric template protection[J]. Chinese Journal of Scientific Instrument, 33, 2767-2773(2012).
[22] Cao J, Zhao X L, Wang J H. Gesture recognition method based on improved finger tip and Hu moments[J]. Computer Engineering and Applications, 53, 138-143, 194(2017).
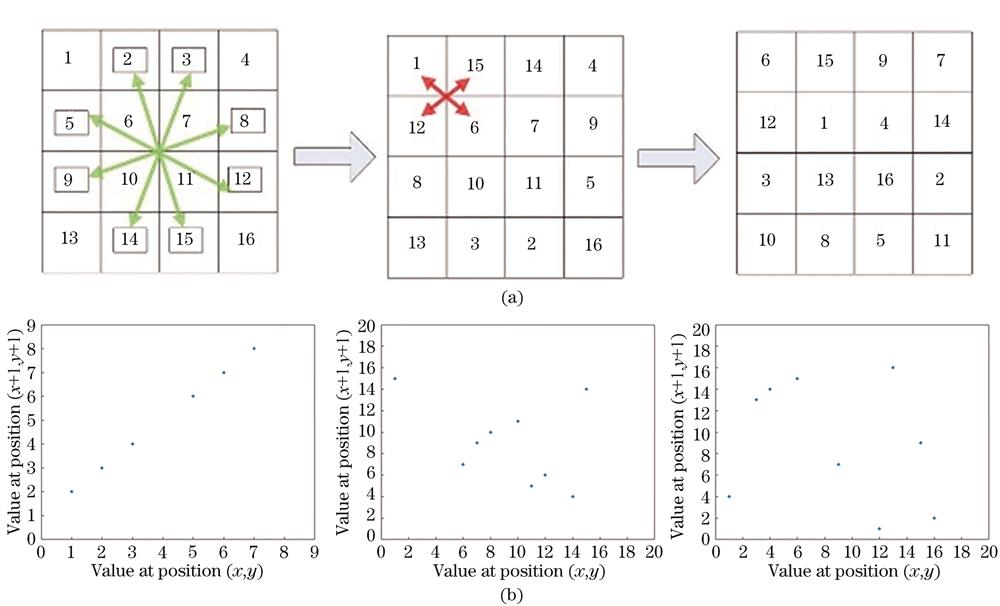
[26] Hu K Y, Wang J, Wang Y. Image encryption based on block compression sensing and the improved magic square transformation[J]. Laser Technology, 43, 96-102(2019).
[27] Li K, Zhang T. Application of logistic mapping in digital image encryption algorithm[J]. Information & Communications, 30, 139-140(2017).
[28] Zhao Y. Image encryption of chaotic system based on shuffle algorithm[D](2019).
[29] Yao L P, Pan Z L. Research on face recognition method based on improved HOG and LBP algorithms[J]. Optoelectronic Technology, 40, 114-118, 124(2020).
[30] Wang Y, Li X. Face recognition based on LDP feature and Bayesian model[J]. Computer Science, 44, 283-286, 291(2017).
[31] Wu L F, Jiang S Y, Xiao P et al. Noninvertible transformation schemes for face template protection[J]. Signal Processing, 28, 1006-1013(2012).