Xue Wang, Zhuhong Shao, Yunfei Wang, Yuanyuan Shang. Color Image Encryption Based on Symmetry of Fourier Transform and R-MRSVD[J]. Laser & Optoelectronics Progress, 2021, 58(4): 0410021
Search by keywords or author
- Laser & Optoelectronics Progress
- Vol. 58, Issue 4, 0410021 (2021)
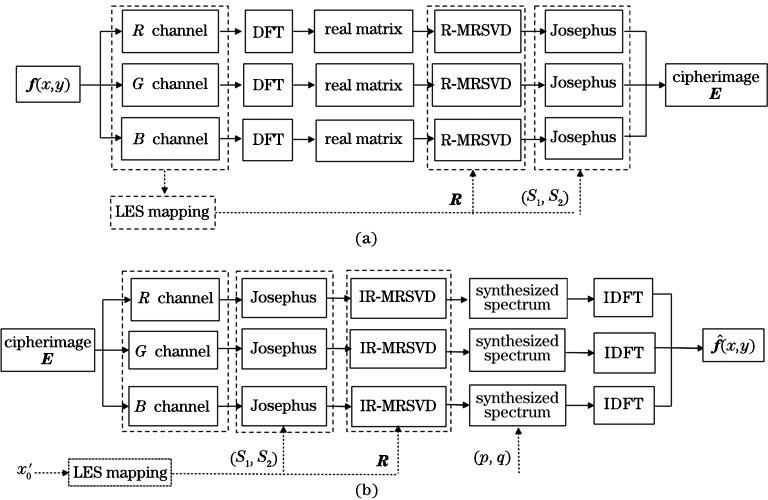
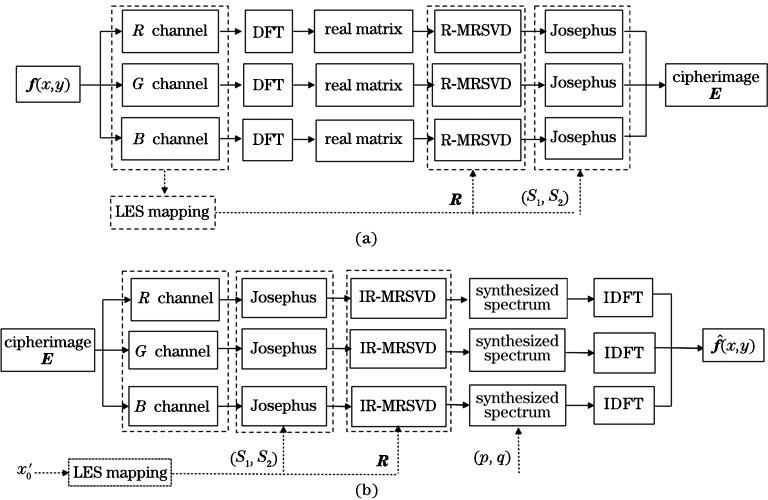
Fig. 1. Flowchart of the proposed algorithm. (a) Encryption process; (b) decryption process
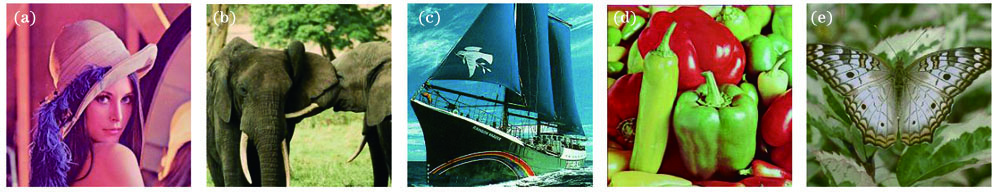
Fig. 2. Tested images. (a) Lena; (b) Elephant; (c) Grnpeace; (d) Peppers; (e) Butterfly
Fig. 3. Results of encryption and decryption. (a) Cipherimages; (b) restituted images
Fig. 4. Histogram results. (a) Plaintext images; (b) ciphertext images
Fig. 5. Correlation distribution of adjacent pixels. (a) Lena's plaintext image; (b) Lena's ciphertext image
Fig. 6. Results of chosen-plaintext attack. (a) Fake plaintext images; (b) decrypted results of Fig.3 (a)
Fig. 7. Decrypted results using a slightly deviated key. (a) a; (b) b; (c) c; (d) x'0
Fig. 8. Decrypted results when the intensity of Gaussian noise is 1. (a) Proposed algorithm; (b) algorithm in Ref.[16]; (c) algorithm in Ref.[17]
Fig. 9. Average PSNR and CC under Gaussian noise attack. (a) PSNR; (b) CC
Fig. 10. Decrypted images under cropping attack(η=20%). (a) Proposed algorithm; (b) algorithm in Ref.[16]; (c) algorithm in Ref.[17]
Fig. 11. Average PSNR and CC under cropping attack. (a) PSNR; (b) CC
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Table 1. PSNR of correctly decryption
|
Table 2. Correlation coefficients of plaintext and ciphertext images
Set citation alerts for the article
Please enter your email address



