Yihang Peng, Wujian Ye, Yijun Liu. Tampered Image Recognition Algorithm Based on Progressive Hybrid Feature[J]. Laser & Optoelectronics Progress, 2022, 59(2): 0211001
Search by keywords or author
- Laser & Optoelectronics Progress
- Vol. 59, Issue 2, 0211001 (2022)
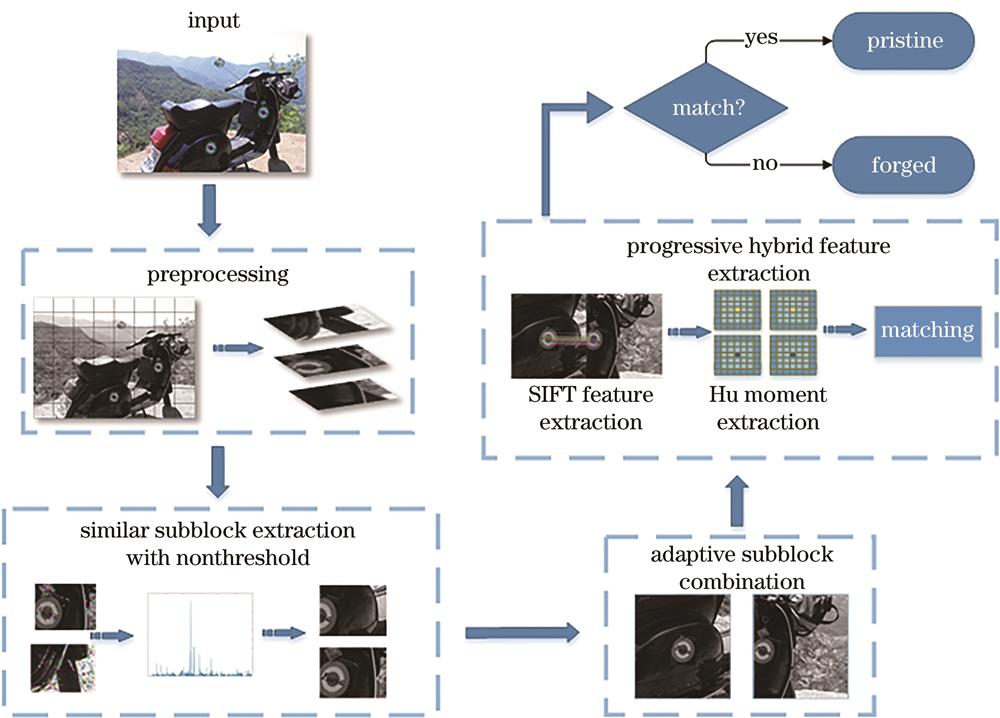
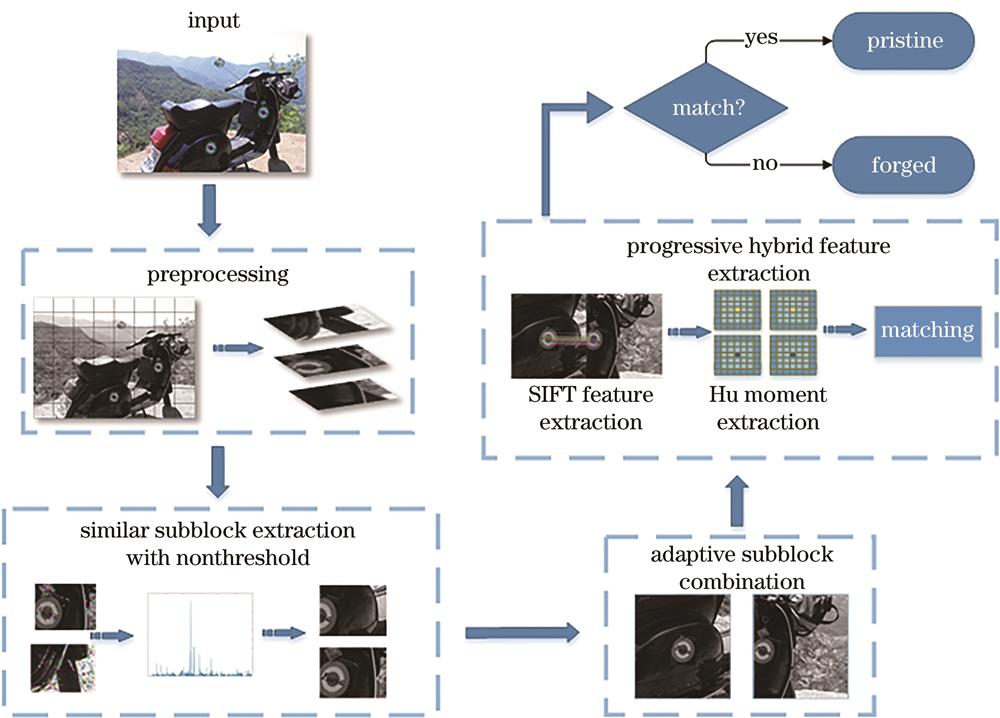
Fig. 1. Flow chart of proposed algorithm
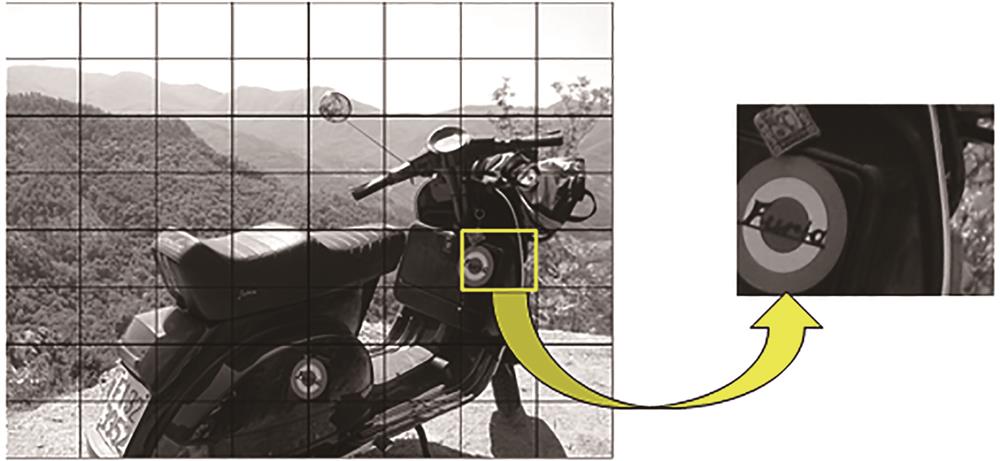
Fig. 2. Non-overlapping uniform segmentation
Fig. 3. Similar sub-block extraction process of Soni algorithm
Fig. 4. Similar sub-block extraction process with non-threshold
Fig. 5. Adaptive sub-block combination. (a) Label for each sub-block; (b) sub-block on edge; (c) case of n=6; (d) case of n=8
Fig. 6. Natural similar areas
Fig. 7. Progressive hybrid feature extraction
Fig. 8. Robust test in MICC-F220
Fig. 9. Robust test in MICC-F2000
Fig. 10. Comparison of results on MICC-F220 dataset
Fig. 11. Comparison of results on MICC-F2000 dataset
|
Table 1. Type of geometric attack in MICC-F220 dataset
|
Table 2. Type of geometric attack in MICC-F2000 dataset
|
Table 3. Attack type
|
Table 4. Experimental results of each stage
|
Table 5. Comparison of running time
|
Table 6. Performance comparison between proposed algorithm and CKN algorithm
Set citation alerts for the article
Please enter your email address



