Guangmang Cui, Kuaikuai Yu, Xiaojie Ye, Jufeng Zhao, Liyao Zhu. Searching Method for Optimal Code Sequence of Coded Exposure Based on Memetic Algorithm[J]. Acta Optica Sinica, 2019, 39(3): 0311004
Search by keywords or author
- Acta Optica Sinica
- Vol. 39, Issue 3, 0311004 (2019)
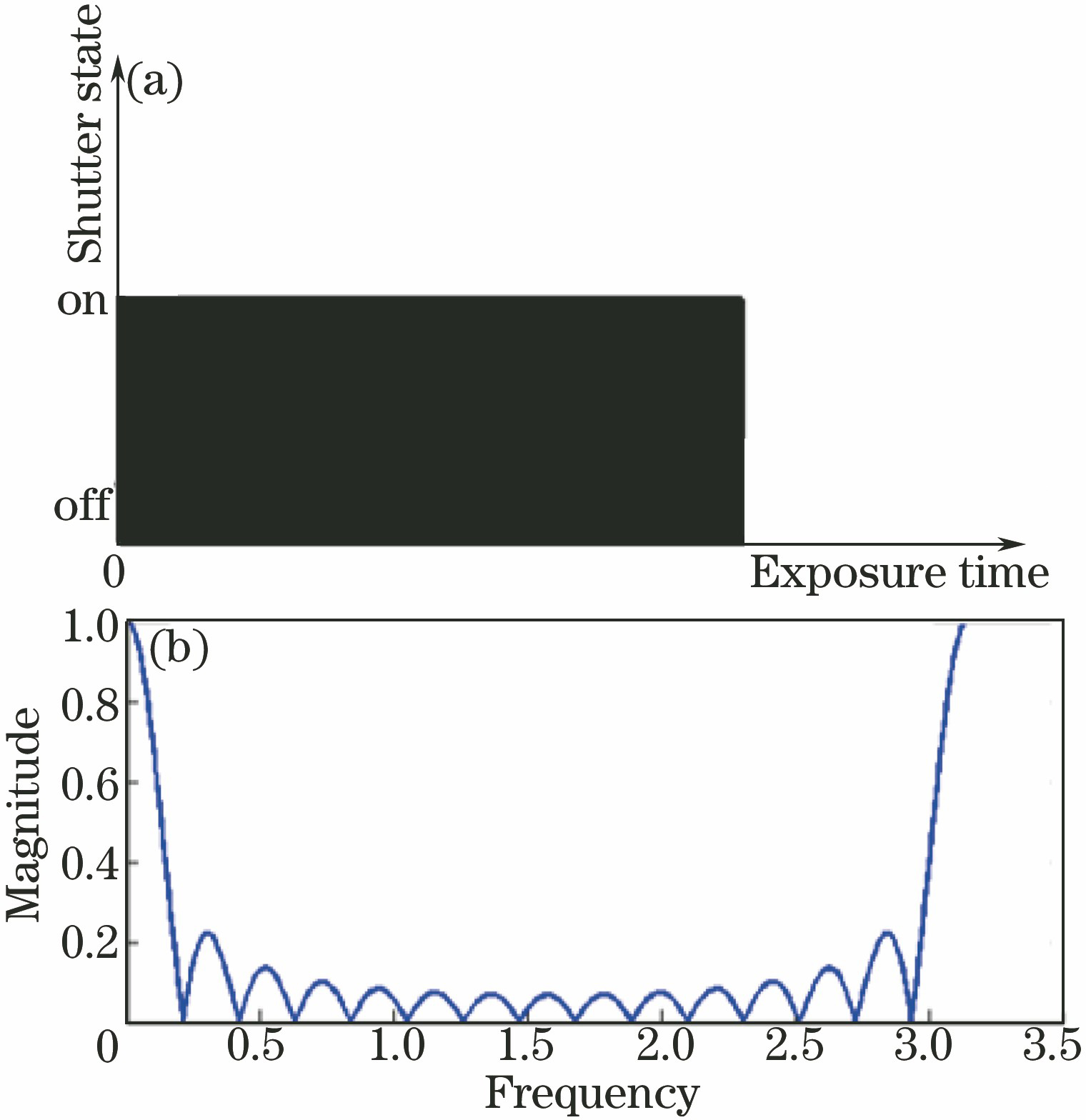
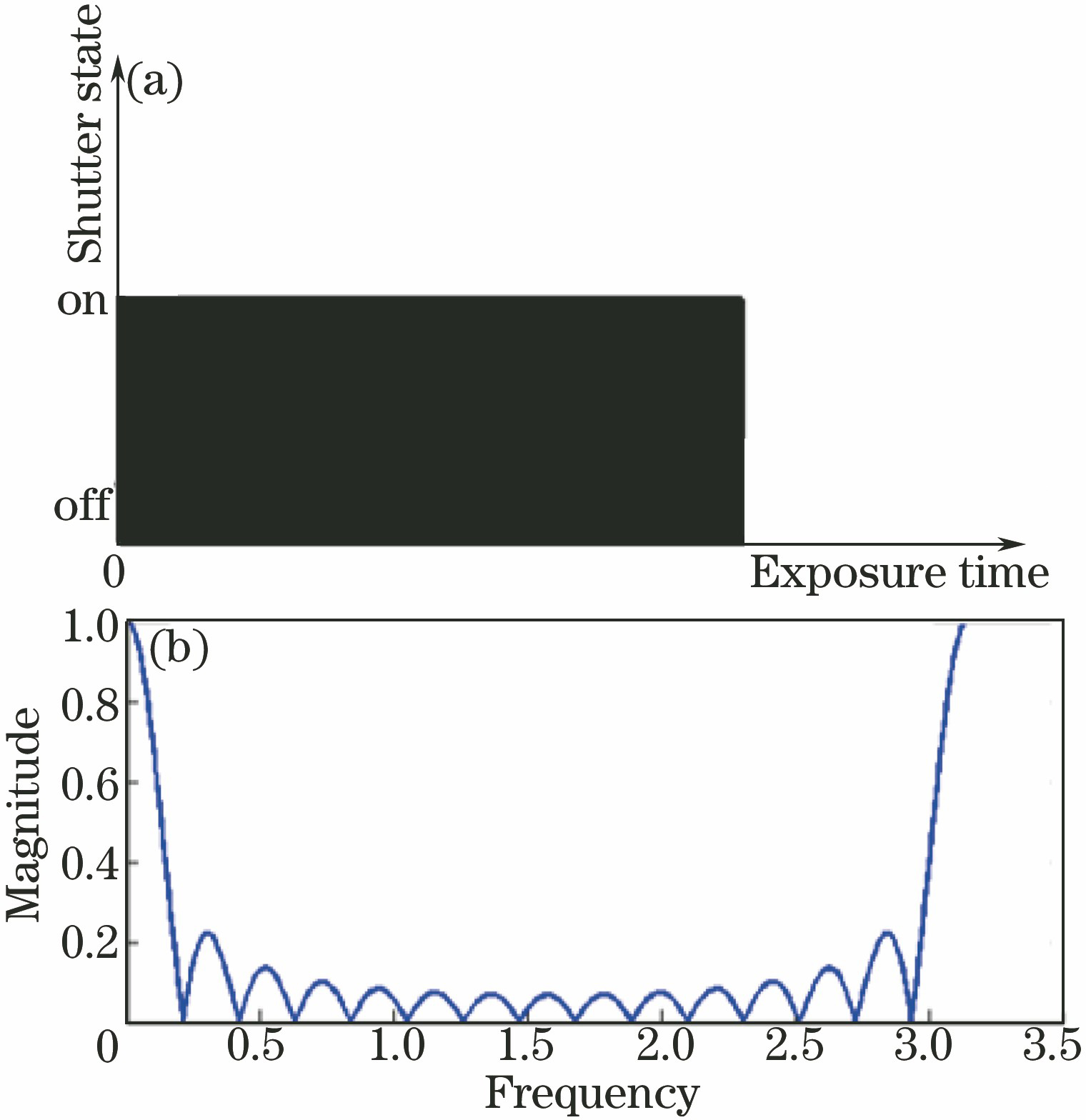
Fig. 1. Traditional exposure mode. (a) Imaging exposure model; (b) Fourier transform amplitude curve
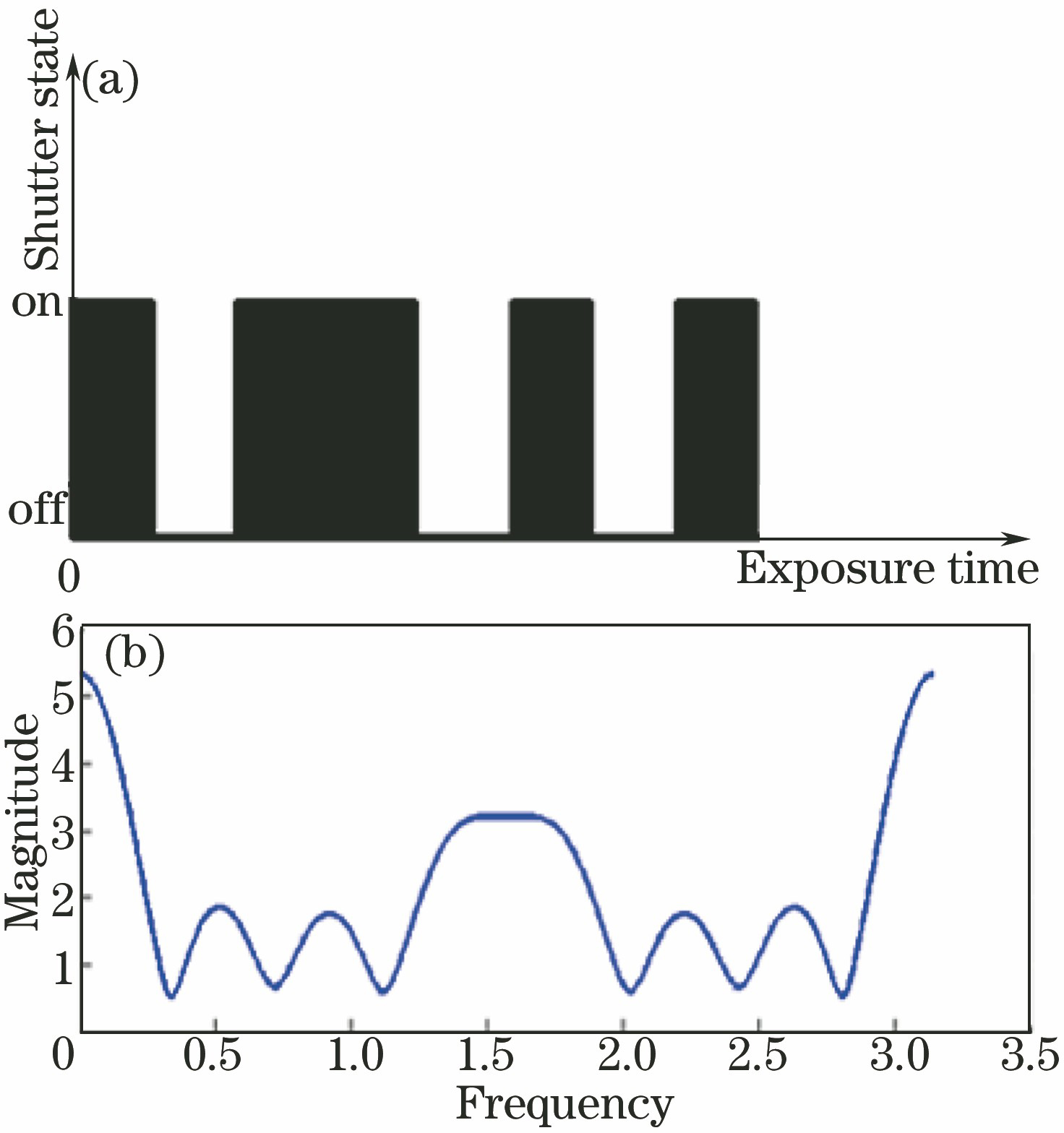
Fig. 2. Coded exposure mode. (a) Coded exposure imaging model; (b) Fourier transform amplitude curve
Fig. 3. Searching method for optimal code sequence of coded exposure based on Memetic algorithm
Fig. 4. Comparison of frequency amplitude curves for code sequence of 32 bits
Fig. 5. Comparison of frequency amplitude curves for code sequence of 52 bits
Fig. 6. Comparison of frequency amplitude curves for code sequence of 112 bits
Fig. 7. Simulated blurred images and deblurring results for image “Target” with code sequence of 32 bits. (a) Traditional exposure mode; (b) coded exposure mode plus genetic search method; (c) coded exposure mode plus Memetic searching method
Fig. 8. Simulated blurred images and deblurring results for image “Target” with code sequence of 32 bits. (a) Traditional exposure mode; (b) coded exposure mode plus genetic search method; (c) coded exposure mode plus Memetic searching method
Fig. 9. Simulated blurred images and deblurring results for image “Cameraman” with code sequence of 32 bits. (a)Traditional exposure mode; (b) coded exposure mode plus genetic search method; (c) coded exposure mode plus Memetic searching method
Fig. 10. Simulated blurred images and deblurring results for image “Cameraman” with code sequence of 52 bits. (a) Traditional exposure mode; (b) coded exposure mode plus genetic search method; (c) coded exposure mode plus Memetic searching method
|
Table 1. Objective evaluation results of frequency amplitude curves for code sequence
|
Table 2. Execution time of searching methods for optimal code sequences
|
Table 3. Objective evaluation results of simulated deblurring images for image “Target”
|
Table 4. Objective evaluation results of simulated deblurring images for image “Cameraman”
Set citation alerts for the article
Please enter your email address



