[1] Mayers D. Unconditional security in quantum cryptography[J]. Journal of the ACM, 48, 351-406(2001).
[2] Gottesman D, Lo H, Lutkenhaus N et al. Security of quantum key distribution with imperfect devices. [C]//International Symposium on Information Theory, June 27-July 2, 2004, Chicago, IL, USA. New York: IEEE, 8178599(2003).
[3] Bennett C H, Brassard G. An update on quantum cryptography[M]. //Blakley G R, Chaum D. Advances in Cryptology. Lecture Notes in Computer Science. Berlin: Springer, 196, 475-480(1984).
[4] Bennett C H, Brassard G, Ekert A K. Quantum cryptography[J]. Scientific American, 267, 50-57(1992).
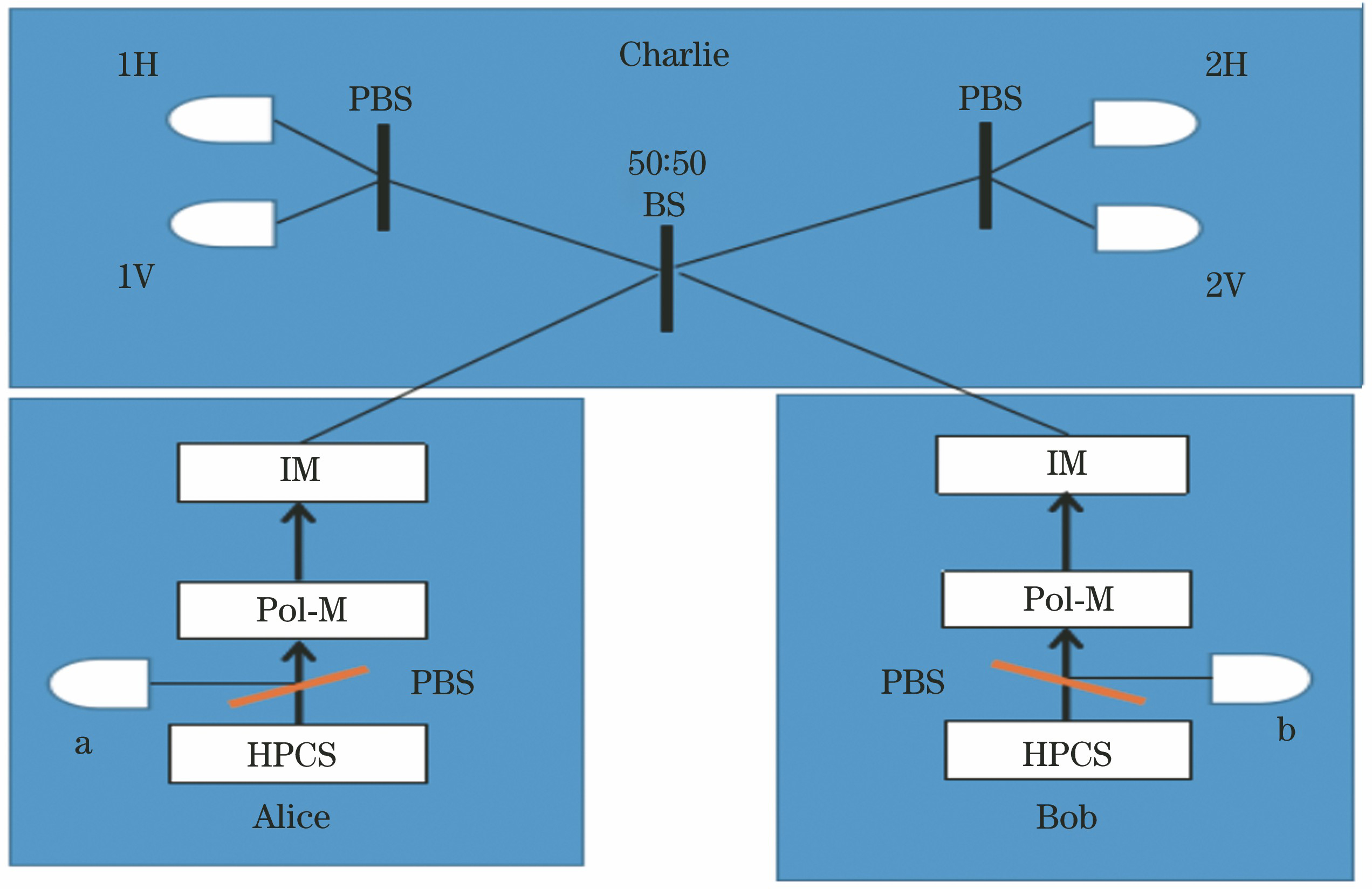
[5] Wang Q, Wang X B. Efficient implementation of the decoy-state measurement-device-independent quantum key distribution with heralded single-photon sources[J]. Physical Review A, 88, 052332(2013).
[7] Brassard G, Lütkenhaus N, Mor T et al. Limitations on practical quantum cryptography[J]. Physical Review Letters, 85, 1330-1333(2000).
[8] Zhao Y, Fung C HF, Qi B et al. Quantum hacking: experimental demonstration of time-shift attack against practical quantum-key-distribution systems[J]. Physical Review A, 78, 042333(2008).
[9] Sun S H, Liang L M. Experimental demonstration of an active phase randomization and monitor module for quantum key distribution[J]. Applied Physics Letters, 101, 071107(2012).
[10] Makarov V, Skaar J. Faked states attack using detector efficiency mismatch on SARG04, phase-time, DPSK, and Ekert protocols[J]. Quantum Information & Computation, 8, 0622-0635(2007).
[11] Lo H K, Curty M, Qi B. Measurement-device-independent quantum key distribution[J]. Physical Review Letters, 108, 130503(2012).
[12] Dong C, Zhao S H, Zhang N et al. Measurement-device-independent quantum key distribution with odd coherent state[J]. Acta Physica Sinica, 63, 200304(2014).
[13] Sun S H, Gao M, Li C Y et al. Practical decoy-state measurement-device-independent quantum key distribution[J]. Physical Review A, 87, 052329(2013).
[15] Zhu Z D, Zhao S H, Wang X Y et al. Phase modulate free measurement device independent quantum key distribution[J]. Journal of Optoelectronics·Laser, 29, 181-186(2018).
[16] Tamaki K, Lo H K. Fung C H Fred, et al. Phase encoding schemes for measurement-device-independent quantum key distribution with basis-dependent flaw[J]. Physical Review A, 85, 042307(2012).
[17] Abruzzo S, Kampermann H, Bruss D. Measurement-device-independent quantum key distribution with quantum memories[J]. Physical Review A, 89, 012301(2013).
[22] Zhang S L, Zou X B, Li C F et al. A universal coherent source for quantum key distribution[J]. Science Bulletin, 54, 1863-1871(2009).
[23] Wang X, Wang Y, Chen R K et al. Measurement-device-independent quantum key distribution with heralded pair coherent state[J]. Laser Physics, 26, 065203(2016).
[25] Yu Z W, Zhou Y H, Wang X B. Statistical fluctuation analysis for measurement-device- independent quantum key distribution with three-intensity decoy-state method[J]. Physical Review A, 91, 032318(2015).
[26] Zhou X Y, Zhang C H, Guo G C et al. The statistical fluctuation analysis for the measurement-device-independent quantum key distribution with heralded single-photon sources[J]. Quantum Information Processing, 15, 2455-2464(2016).
[27] Zhou Y Y, Zhang H Q, Zhou X J et al. Analysis of the performance of decoy quantum key distribution based on heralded paired coherent state light source[J]. Acta Physica Sinica, 62, 200302(2013).
[28] Dong C, Zhao S H, Shi L. Measurement device-independent quantum key distribution with heralded pair coherent state[J]. Quantum Information Processing, 15, 4253-4263(2016).
[29] Ma X F, Razavi M. Alternative schemes for measurement-device-independent quantum key distribution[J]. Physical Review A, 86, 062319(2012).