[1] Liu D M, Sun Q Z, Lu P et al. Research progress in the key device and technology for fiber optic sensor network[J]. Photonic Sensors, 6, 1-25(2016). http://link.springer.com/article/10.1007/s13320-015-0299-z
Liu D M, Sun Q Z, Lu P et al. Research progress in the key device and technology for fiber optic sensor network[J]. Photonic Sensors, 6, 1-25(2016). http://link.springer.com/article/10.1007/s13320-015-0299-z
[2] Allwood G, Wild G, Hinckley S. Optical fiber sensors in physical intrusion detection systems: a review[J]. IEEE Sensors Journal, 16, 5497-5509(2016). http://ieeexplore.ieee.org/document/7421944
Allwood G, Wild G, Hinckley S. Optical fiber sensors in physical intrusion detection systems: a review[J]. IEEE Sensors Journal, 16, 5497-5509(2016). http://ieeexplore.ieee.org/document/7421944
[3] Huang S C, Lin W W, Tsai M T et al. Fiber optic in-line distributed sensor for detection and localization of the pipeline leaks[J]. Sensors and Actuators A: Physical, 135, 570-579(2007). http://www.sciencedirect.com/science/article/pii/S092442470600625X
Huang S C, Lin W W, Tsai M T et al. Fiber optic in-line distributed sensor for detection and localization of the pipeline leaks[J]. Sensors and Actuators A: Physical, 135, 570-579(2007). http://www.sciencedirect.com/science/article/pii/S092442470600625X
[4] Lopez-Higuera J M, Rodriguez Cobo L, Quintela Incera A et al. . Fiber optic sensors in structural health monitoring[J]. Journal of Lightwave Technology, 29, 587-608(2011). http://ieeexplore.ieee.org/document/5709958
Lopez-Higuera J M, Rodriguez Cobo L, Quintela Incera A et al. . Fiber optic sensors in structural health monitoring[J]. Journal of Lightwave Technology, 29, 587-608(2011). http://ieeexplore.ieee.org/document/5709958
[5] Liao Y B, Yuan L B, Tian Q. The 40 years of optical fiber sensors in China[J]. Acta Optica Sinica, 38, 0328001(2018).
Liao Y B, Yuan L B, Tian Q. The 40 years of optical fiber sensors in China[J]. Acta Optica Sinica, 38, 0328001(2018).
[6] Li P C, Liu K, Jiang J F et al. Research on polarization control of distributed optical fiber sensing system based on FPGA[J]. Chinese Journal of Lasers, 45, 0510002(2018).
Li P C, Liu K, Jiang J F et al. Research on polarization control of distributed optical fiber sensing system based on FPGA[J]. Chinese Journal of Lasers, 45, 0510002(2018).
[7] Ghafoori-Shiraz H, Okoshi T. Fault location in optical fibers using optical frequency domain reflectometry[J]. Journal of Lightwave Technology, 4, 316-322(1986). http://ieeexplore.ieee.org/xpls/abs_all.jsp?arnumber=1074720
Ghafoori-Shiraz H, Okoshi T. Fault location in optical fibers using optical frequency domain reflectometry[J]. Journal of Lightwave Technology, 4, 316-322(1986). http://ieeexplore.ieee.org/xpls/abs_all.jsp?arnumber=1074720
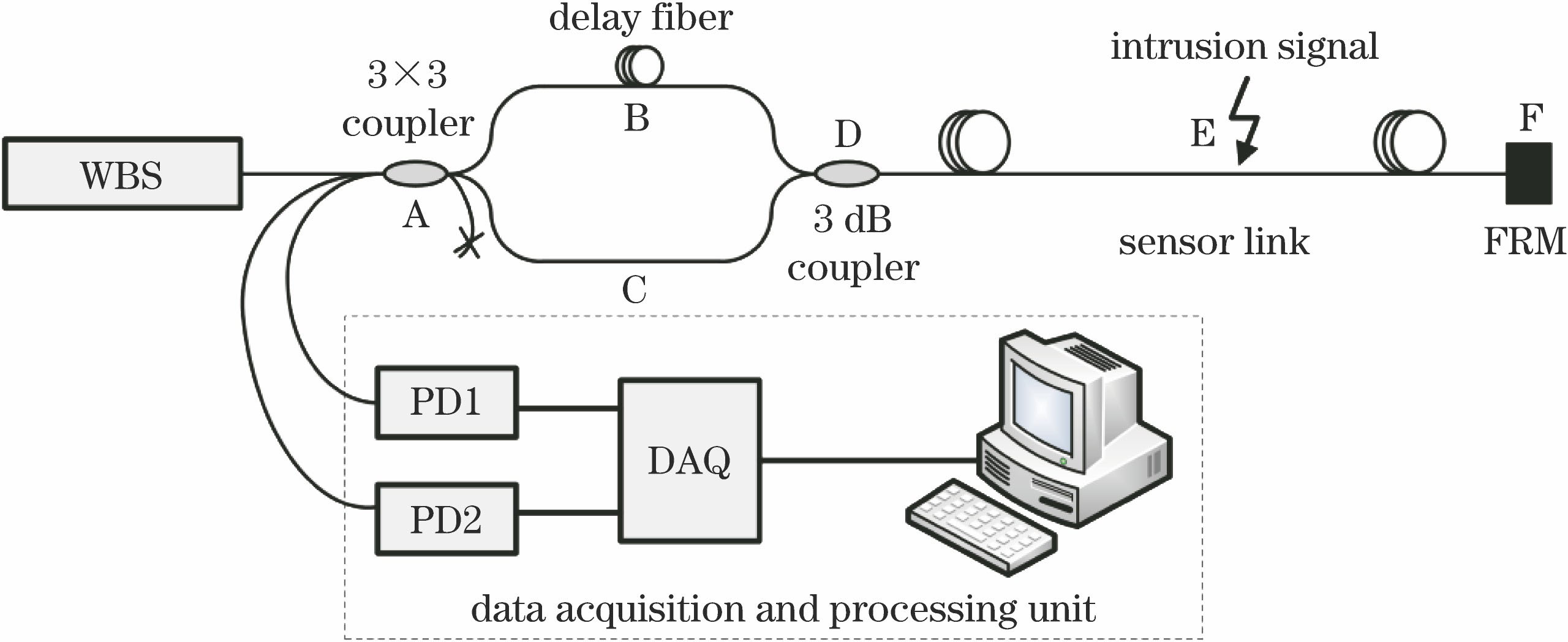
[8] Huang X D, Wang Y D, Liu K et al. Event discrimination of fiber disturbance based on filter bank in DMZI sensing system[J]. IEEE Photonics Journal, 8, 1-14(2016). http://ieeexplore.ieee.org/document/7450616/
Huang X D, Wang Y D, Liu K et al. Event discrimination of fiber disturbance based on filter bank in DMZI sensing system[J]. IEEE Photonics Journal, 8, 1-14(2016). http://ieeexplore.ieee.org/document/7450616/
[9] Liu K, Tian M, Liu T G et al. A high-efficiency multiple events discrimination method in optical fiber perimeter security system[J]. Journal of Lightwave Technology, 33, 4885-4890(2015). http://ieeexplore.ieee.org/document/7305775/
Liu K, Tian M, Liu T G et al. A high-efficiency multiple events discrimination method in optical fiber perimeter security system[J]. Journal of Lightwave Technology, 33, 4885-4890(2015). http://ieeexplore.ieee.org/document/7305775/
[10] Jiang L H, Gai J Y, Wang W B et al. Ensemble empirical mode decomposition based event classification method for the fiber-optic intrusion monitoring system[J]. Acta Optica Sinica, 35, 1006002(2015).
Jiang L H, Gai J Y, Wang W B et al. Ensemble empirical mode decomposition based event classification method for the fiber-optic intrusion monitoring system[J]. Acta Optica Sinica, 35, 1006002(2015).
[11] Jiang L H, Liu X M, Yang R Y. Application of the HHT method to the airport fiber fence warning. [C]∥2011 International Conference on Electronics, Communications and Control (ICECC), September 9-11, 2011, Ningbo, China. New York: IEEE, 1337-1340(2011).
Jiang L H, Liu X M, Yang R Y. Application of the HHT method to the airport fiber fence warning. [C]∥2011 International Conference on Electronics, Communications and Control (ICECC), September 9-11, 2011, Ningbo, China. New York: IEEE, 1337-1340(2011).
[12] Mahmoud S S, Visagathilagar Y, Katsifolis J. Real-time distributed fiber optic sensor for security systems: performance, event classification and nuisance mitigation[J]. Photonic Sensors, 2, 225-236(2012). http://www.opticsjournal.net/Articles/Abstract?aid=OJ130416000212KhNjQm
Mahmoud S S, Visagathilagar Y, Katsifolis J. Real-time distributed fiber optic sensor for security systems: performance, event classification and nuisance mitigation[J]. Photonic Sensors, 2, 225-236(2012). http://www.opticsjournal.net/Articles/Abstract?aid=OJ130416000212KhNjQm
[13] Li K Y, Zhao X Q, Sun X H et al. A regular composite feature extraction method for vibration signal pattern recognition in optical fiber link system[J]. Acta Physica Sinica, 64, 054304(2015).
Li K Y, Zhao X Q, Sun X H et al. A regular composite feature extraction method for vibration signal pattern recognition in optical fiber link system[J]. Acta Physica Sinica, 64, 054304(2015).
[14] Huang X D, Zhang H J, Liu K et al. High-efficiency intrusion recognition by using synthesized features in optical fiber perimeter security system[J]. Acta Physica Sinica, 66, 124206(2017).
Huang X D, Zhang H J, Liu K et al. High-efficiency intrusion recognition by using synthesized features in optical fiber perimeter security system[J]. Acta Physica Sinica, 66, 124206(2017).
[15] Wang H, Sun Q Z, Li X L et al. Improved location algorithm for multiple intrusions in distributed Sagnac fiber sensing system[J]. Optics Express, 22, 7587-7597(2014). http://www.opticsinfobase.org/abstract.cfm?URI=oe-22-7-7587
Wang H, Sun Q Z, Li X L et al. Improved location algorithm for multiple intrusions in distributed Sagnac fiber sensing system[J]. Optics Express, 22, 7587-7597(2014). http://www.opticsinfobase.org/abstract.cfm?URI=oe-22-7-7587
[16] Donoho D L. De-noising by soft-thresholding[J]. IEEE Transactions on Information Theory, 41, 613-627(1995). http://dl.acm.org/citation.cfm?id=2274414
Donoho D L. De-noising by soft-thresholding[J]. IEEE Transactions on Information Theory, 41, 613-627(1995). http://dl.acm.org/citation.cfm?id=2274414
[17] Jansen M. Noise reduction by wavelet thresholding[M]. New York: Springer-Verlag, 35-39(2001).
Jansen M. Noise reduction by wavelet thresholding[M]. New York: Springer-Verlag, 35-39(2001).
[18] Hu G S[M]. Modern digital signal processing tutorial, 381-388(2015).
Hu G S[M]. Modern digital signal processing tutorial, 381-388(2015).
[19] Han L H, Wang B, Duan S F. Development of voice activity detection technology[J]. Application Research of Computers, 27, 1220-1226(2010).
Han L H, Wang B, Duan S F. Development of voice activity detection technology[J]. Application Research of Computers, 27, 1220-1226(2010).
[20] Tanyer S G, Ozer H. Voice activity detection in nonstationary noise[J]. IEEE Transactions on Speech and Audio Processing, 8, 478-482(2000). http://ieeexplore.ieee.org/xpls/abs_all.jsp?arnumber=848229
Tanyer S G, Ozer H. Voice activity detection in nonstationary noise[J]. IEEE Transactions on Speech and Audio Processing, 8, 478-482(2000). http://ieeexplore.ieee.org/xpls/abs_all.jsp?arnumber=848229
[21] Jain A K. Duin R P W, Mao J C. Statistical pattern recognition: a review[J]. IEEE Transactions on Pattern Analysis and Machine Intelligence, 22, 4-37(2000).
Jain A K. Duin R P W, Mao J C. Statistical pattern recognition: a review[J]. IEEE Transactions on Pattern Analysis and Machine Intelligence, 22, 4-37(2000).
[22] Liu L, Sun W, Zhou Y et al. Security event classification method for fiber-optic perimeter security system based on optimized incremental support vector machine[M]. ∥Li S, Liu C, Wang Y. Communications in Computer and Information Science. Berlin, Heidelberg: Springer, 595-603(2014).
Liu L, Sun W, Zhou Y et al. Security event classification method for fiber-optic perimeter security system based on optimized incremental support vector machine[M]. ∥Li S, Liu C, Wang Y. Communications in Computer and Information Science. Berlin, Heidelberg: Springer, 595-603(2014).
[23] Wang L K, Tan D J, Cai Y J et al. Study on method of recognizing characteristics of pipeline leakage acoustic signals. [C]∥Pipeline Division. 2006 International Pipeline Conference, September 25-29, 2006, Calgary, Alberta, Canada. New York: ASME, 751-755(2006).
Wang L K, Tan D J, Cai Y J et al. Study on method of recognizing characteristics of pipeline leakage acoustic signals. [C]∥Pipeline Division. 2006 International Pipeline Conference, September 25-29, 2006, Calgary, Alberta, Canada. New York: ASME, 751-755(2006).
[24] Sun J D, Jin S J. Feature extraction method based on wavelet packet energy and high-order spectrum[J]. Journal of Tianjin University, 43, 562-566(2010).
Sun J D, Jin S J. Feature extraction method based on wavelet packet energy and high-order spectrum[J]. Journal of Tianjin University, 43, 562-566(2010).
[25] Haykin S, Simon Haykin[M]. 神经网络与机器学习, 144-193(2011).
Haykin S, Simon Haykin[M]. 神经网络与机器学习, 144-193(2011).
[M]. Neural networks and learning machines, 144-193(2011).
[M]. Neural networks and learning machines, 144-193(2011).
[26] Hsu C W, Lin C J. A comparison of methods for multiclass support vector machines[J]. IEEE Transactions on Neural Networks, 13, 415-425(2002). http://www.tandfonline.com/servlet/linkout?suffix=CIT0024&dbid=16&doi=10.1080%2F15481603.2018.1426091&key=10.1109%2F72.991427
Hsu C W, Lin C J. A comparison of methods for multiclass support vector machines[J]. IEEE Transactions on Neural Networks, 13, 415-425(2002). http://www.tandfonline.com/servlet/linkout?suffix=CIT0024&dbid=16&doi=10.1080%2F15481603.2018.1426091&key=10.1109%2F72.991427
[27] Lingras P, Butz C. Rough set based 1-v-1 and 1-v-r approaches to support vector machine multi-classification[J]. Information Sciences, 177, 3782-3798(2007). http://www.sciencedirect.com/science/article/pii/S0020025507001594
Lingras P, Butz C. Rough set based 1-v-1 and 1-v-r approaches to support vector machine multi-classification[J]. Information Sciences, 177, 3782-3798(2007). http://www.sciencedirect.com/science/article/pii/S0020025507001594
[28] Li Y C, Xue Q, Fu X J. Analysis on features of stealing oil signal of pipeline with wavelet transform[J]. Journal of Wuhan University of Technology, 32, 76-79, 94(2010).
Li Y C, Xue Q, Fu X J. Analysis on features of stealing oil signal of pipeline with wavelet transform[J]. Journal of Wuhan University of Technology, 32, 76-79, 94(2010).