Yu Li, Liming Zhang, Hao Wang, Xiaolong Wang. Commutative Encryption and Watermarking Algorithm for High-Resolution Remote Sensing Images Based on Homomorphic Encryption[J]. Laser & Optoelectronics Progress, 2022, 59(18): 1815012
Search by keywords or author
- Laser & Optoelectronics Progress
- Vol. 59, Issue 18, 1815012 (2022)
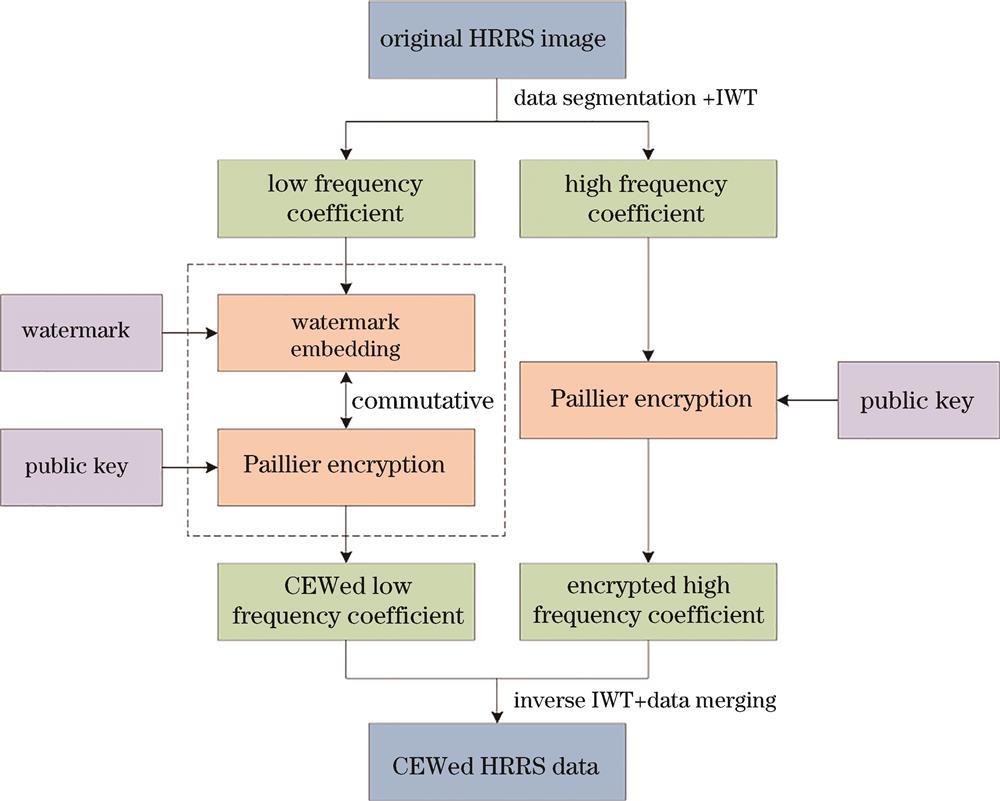
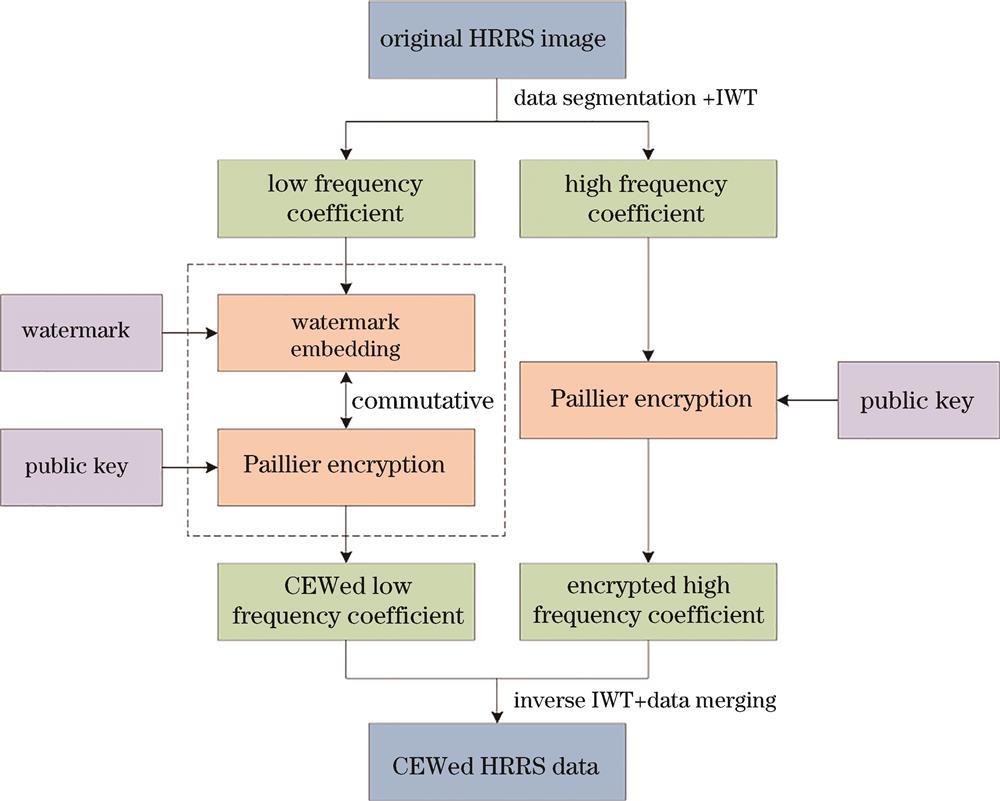
Fig. 1. CEW algorithm model for HRRS image
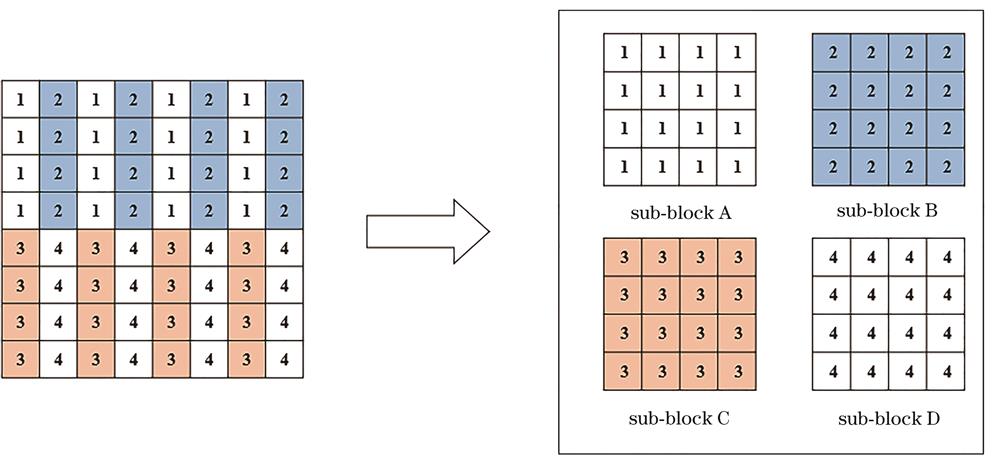
Fig. 2. Division of HRRS image
Fig. 3. Original images. (a) Image A; (b) image B; (c) image C
Fig. 4. Watermark images. (a) Original watermark; (b) shuffled watermark
Fig. 5. CEW experiment results. (a)-(c) CEWed image (A1, B1, C1); (d)-(f) D-Wed image (A2, B2, C2)
Fig. 6. Analysis result of key sensitivity. (a)-(c) CEWed image (A3, B3, C3) with the key pk2; (d)-(f) D-Wed image (A4, B4, C4) with sk2
Fig. 7. Comparison result of imperceptibility
Fig. 8. Comparison result of robustness
|
Table 1. MAE of CEWed/D-Wed images using different secret keys
| ||||||||||||||||||||||||||||||||||
Table 2. Adjacent pixel correlation between original images and encrypted images
|
Table 3. PSNR of D-Wed images with different embedding intensities
| ||||||||||||||||||||||||||||||||||||||||
Table 4. Experimental results of robustness
| |||||||||||||||||||||||||||
Table 5. Comparison of algorithm running time
|
Table 6. Result of accuracy evaluation
Set citation alerts for the article
Please enter your email address



