[1] Pittman T B, Shih Y H, Strekalov D V et al. Optical imaging by means of two-photon quantum entanglement[J]. Physical Review A, 52, R3429-R3432(1995). http://europepmc.org/abstract/med/9912767
[2] Strekalov D V, Sergienko A V, Klyshko D N et al. Observation of two-photon “ghost” interference and diffraction[J]. Physical Review Letters, 74, 3600-3603(1995).
[3] Bennink R S, Bentley S J, Boyd R W. “Two-photon” coincidence imaging with a classical source[J]. Physical Review Letters, 89, 113601(2002). http://europepmc.org/abstract/MED/12225140
[4] Valencia A, Scarcelli G, D’Angelo M et al. Two-photon imaging with thermal light[J]. Physical Review Letters, 94, 063601(2005).
[5] Zhai Y H, Chen X H, Zhang D et al. Two-photon interference with true thermal light[J]. Physical Review A, 72, 043805(2005). http://arxiv.org/abs/quant-ph/0506056
[6] Liu H L, Shen X, Zhu D M et al. Fourier-transform ghost imaging with pure far-field correlated thermal light[J]. Physical Review A, 76, 053808(2007). http://adsabs.harvard.edu/abs/2007PhRvA..76e3808L
[7] Bai Y F, Han S S. Ghost imaging with thermal light by third-order correlation[J]. Physical Review A, 76, 043828(2007). http://adsabs.harvard.edu/abs/2007PhRvA..76d3828B
[8] Liu H L, Han S S. Spatial longitudinal coherence length of a thermal source and its influence on lensless ghost imaging[J]. Optics Letters, 33, 824-826(2008). http://www.opticsinfobase.org/ol/abstract.cfm?uri=ol-33-8-824
[9] Shapiro J H. Computational ghost imaging[J]. Physical Review A, 78, 061802(2008).
[10] Clemente P, Durán V, Tajahuerce E et al. Single-pixel digital ghost holography[J]. Physical Review A, 86, 041803(2012). http://www.oalib.com/paper/3396381
[11] Hardy N D, Shapiro J H. Computational ghost imaging versus imaging laser radar for three-dimensional imaging[J]. Physical Review A, 87, 023820(2013). http://arxiv.org/abs/1212.3253
[12] Gao C, Wang X Q, Wang Z F et al. Optimization of computational ghost imaging[J]. Physical Review A, 96, 023838(2017).
[13] Le M N, Wang G, Zheng H B et al. Underwater computational ghost imaging[J]. Optics Express, 25, 22859-22868(2017). http://europepmc.org/abstract/MED/29041592
[14] Tao Y, Wang X X, Yan G Q et al. Computational ghost imaging method based on Tikhonov regularization[J]. Laser & Optoelectronics Progress, 57, 021016(2020).
[15] Yan G Q, Yang F B, Wang X X et al. Computational ghost imaging based on orthogonal sinusoidal speckle[J]. Laser & Optoelectronics Progress, 57, 041019(2020).
[16] Feng W, Zhao X D, Tang S J et al. Compressive computational ghost imaging method based on region segmentation[J]. Laser & Optoelectronics Progress, 57, 101105(2020).
[17] Clemente P, Durán V, Torres-Company V et al. Optical encryption based on computational ghost imaging[J]. Optics Letters, 35, 2391-2393(2010). http://www.ncbi.nlm.nih.gov/pubmed/20634840
[18] Tanha M, Kheradmand R, Ahmadi-Kandjani S. Gray-scale and color optical encryption based on computational ghost imaging[J]. Applied Physics Letters, 101, 101108(2012). http://scitation.aip.org/content/aip/journal/apl/101/10/10.1063/1.4748875
[19] Chen W, Chen X D. Ghost imaging for three-dimensional optical security[J]. Applied Physics Letters, 103, 221106(2013). http://scitation.aip.org/content/aip/journal/apl/103/22/10.1063/1.4836995
[20] Yu H, Lu R H, Han S S et al. Fourier-transform ghost imaging with hard X rays[J]. Physical Review Letters, 117, 113901(2016).
[21] Pelliccia D, Rack A, Scheel M et al. Experimental X-ray ghost imaging[J]. Physical Review Letters, 117, 113902(2016).
[22] Zhang A X, He Y H, Wu L G et al. Tabletop X-ray ghost imaging with ultra-low radiation[J]. Optica, 5, 374-377(2018). http://arxiv.org/abs/1709.01016
[23] Klein Y, Schori A, Dolbnya I P et al. X-ray computational ghost imaging with single-pixel detector[J]. Optics Express, 27, 3284-3293(2019).
[24] He Y H, Zhang A X, Li M F et al. High-resolution sub-sampling incoherent X-ray imaging with a single-pixel detector[J]. APL Photonics, 5, 056102(2020). http://www.researchgate.net/publication/341146598_High-resolution_sub-sampling_incoherent_x-ray_imaging_with_a_single-pixel_detector
[25] Khakimov R I, Henson B M, Shin D K et al. Ghost imaging with atoms[J]. Nature, 540, 100-103(2016).
[26] Li S, Cropp F, Kabra K et al. Electron ghost imaging[J]. Physical Review Letters, 121, 114801(2018).
[27] Kingston A M, Myers G R, Pelliccia D et al. Neutron ghost imaging[J]. Physical Review A, 101, 053844(2020).
[28] He Y H, Huang Y Y, Zeng Z R et al. Single-pixel imaging with neutrons[J]. Science Bulletin, 66, 133-138(2021). http://www.sciencedirect.com/science/article/pii/S2095927320306265
[29] Ryczkowski P, Barbier M, Friberg A T et al. Ghost imaging in the time domain[J]. Nature Photonics, 10, 167-170(2016). http://www.nature.com/articles/nphoton.2015.274
[30] Devaux F, Moreau P A, Denis S et al. Computational temporal ghost imaging[J]. Optica, 3, 698-701(2016).
[31] Denis S, Moreau P A, Devaux F et al. Temporal ghost imaging with twin photons[J]. Journal of Optics, 19, 034002(2017). http://d.wanfangdata.com.cn/periodical/b853197fb04c54fab85ae26d681bb997
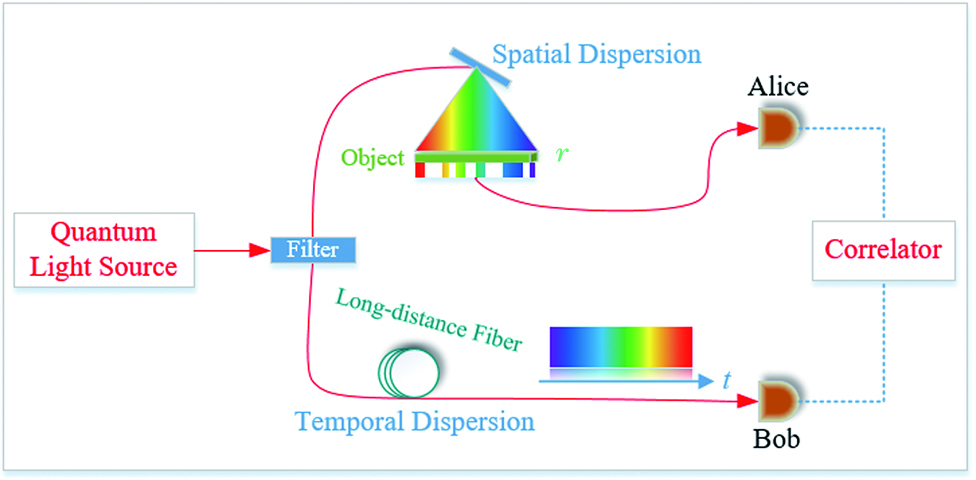
[32] Dong S, Zhang W, Huang Y D et al. Long-distance temporal quantum ghost imaging over optical fibers[J]. Scientific Reports, 6, 26022(2016). http://pubmedcentralcanada.ca/pmcc/articles/PMC4872159/
[33] Yao X, Zhang W, Li H et al. Long-distance thermal temporal ghost imaging over optical fibers[J]. Optics Letters, 43, 759-762(2018). http://www.opticsinfobase.org/abstract.cfm?uri=ol-43-4-759
[34] Gisin N, Ribordy G, Tittel W et al. Quantum cryptography[J]. Reviews of Modern Physics, 74, 145-195(2002).
[35] Scarani V, Bechmann-Pasquinucci H, Cerf N J et al. The security of practical quantum key distribution[J]. Reviews of Modern Physics, 81, 1301-1350(2009). http://scitation.aip.org/getabs/servlet/GetabsServlet?prog=normal&id=VIRT04000009000010000008000001&idtype=cvips&gifs=Yes
[36] Zhong T, Zhou H C, Horansky R D et al. Photon-efficient quantum key distribution using time-energy entanglement with high-dimensional encoding[J]. New Journal of Physics, 17, 022002(2015). http://adsabs.harvard.edu/abs/2015NJPh...17b2002Z
[37] Boaron A, Boso G, Rusca D et al. Secure quantum key distribution over 421 km of optical fiber[J]. Physical Review Letters, 121, 190502(2018). http://arxiv.org/abs/1807.03222v1
[38] Liao S K, Cai W Q, Handsteiner J et al. Satellite-relayed intercontinental quantum network[J]. Physical Review Letters, 120, 030501(2018).
[39] Liu X, Yao X, Wang H Q et al. Energy-time entanglement based dispersive optics quantum key distribution over optical fibers of 20 km[C]. //CLEO: Science and Innovations 2019, May 5-10, 2019, San Jose, California, United States. Washington, D.C.: OSA, JTu2A.33(2019).
[40] Yao X, Liu X, You L X et al. Quantum secure ghost imaging[J]. Physical Review A, 98, 063816(2018).
[41] Franson J D. Bell inequality for position and time[J]. Physical Review Letters, 62, 2205-2208(1989). http://prola.aps.org/abstract/PRL/v62/i19/p2205_1
[42] Yao X, Liu X, Zhang W et al. Multi-bit quantum digital signature based on temporal quantum ghost imaging[C]. //Quantum Information and Measurement(QIM) V: Quantum Technologies, April 4-6, 2019, Rome, ltaly. Washington, D.C.: OSA, T5A.46(2019).
[43] Franson J D. Nonlocal cancellation of dispersion[J]. Physical Review A, 45, 3126-3132(1992). http://www.ncbi.nlm.nih.gov/pubmed/9907348
[44] Lee C, Zhang Z S, Steinbrecher G R et al. Entanglement-based quantum communication secured by nonlocal dispersion cancellation[J]. Physical Review A, 90, 062331(2014). http://adsabs.harvard.edu/abs/2014phrva..90f2331l
[45] Wu J, Wang F X, Chen W et al. Temporal ghost imaging for quantum device evaluation[J]. Optics Letters, 44, 2522-2525(2019). http://www.ncbi.nlm.nih.gov/pubmed/31090722
[46] Wang F X, Wu J, Chen W et al. Perceiving quantum hacking for quantum key distribution using temporal ghost imaging[J]. Physical Review Applied, 15, 034051(2021). http://www.researchgate.net/publication/350147067_Perceiving_Quantum_Hacking_for_Quantum_Key_Distribution_Using_Temporal_Ghost_Imaging