Tao Yu, Dong-Yu Yang, Rui Ma, Yu-Peng Zhu, Yi-Shi Shi. Enhanced-visual-cryptography-based optical information hiding system [J]. Acta Physica Sinica, 2020, 69(14): 144202-1
Search by keywords or author
- Acta Physica Sinica
- Vol. 69, Issue 14, 144202-1 (2020)
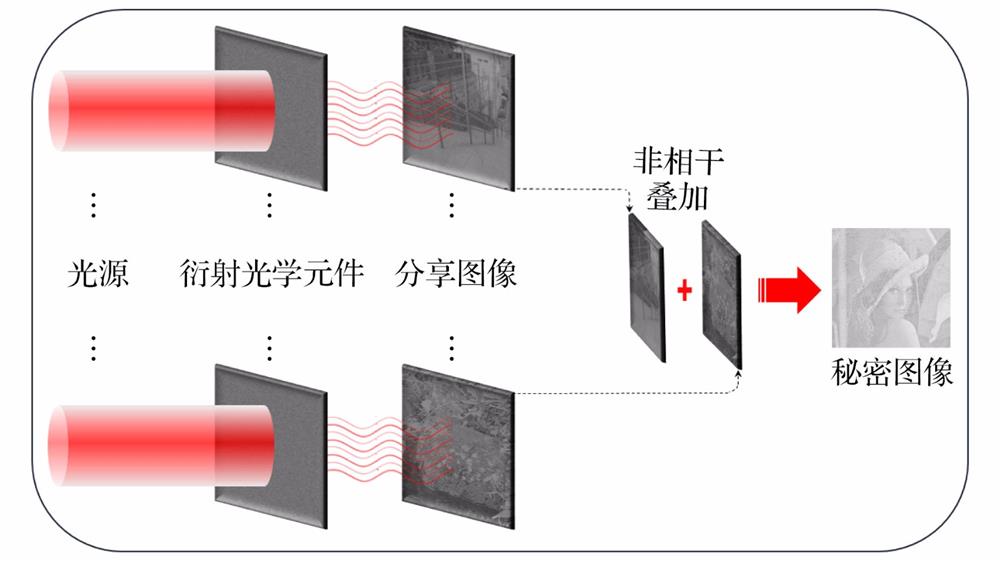
Fig. 1. EVC-based optical hiding system: The extraction process
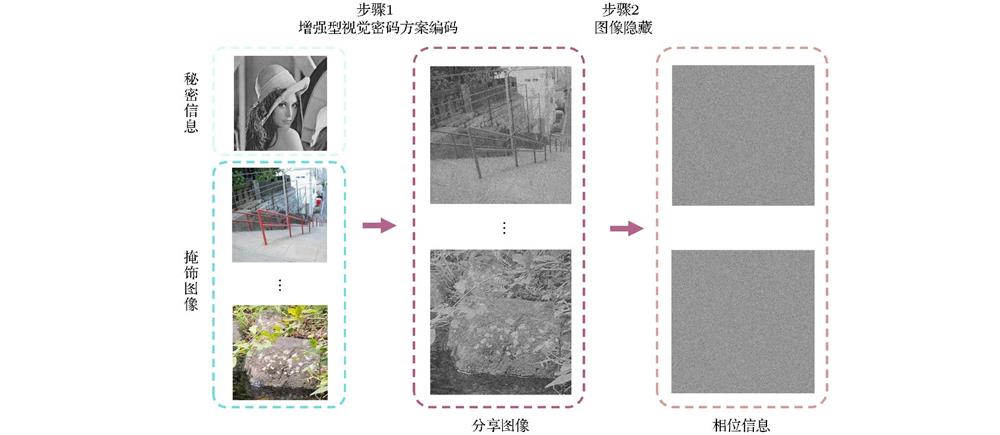
Fig. 2. Extended-visual-cryptographic-based optical hiding system: The hiding process
Fig. 3. Two shares (a), (b) are stacked together to recover the secret information (c)
Fig. 4. Examples of subpixel arrangements. Arranging two subpixels with

 and
and

 as the examples make
as the examples make
 ,
,
 and
and


 and
and

 as the examples make
as the examples make
 ,
,
 and
and

Fig. 5. A example of phase-keys generation algorithms: GS algorithm flow diagram
Fig. 6. (a), (b) The original images of shares; (c) the secret image; (d), (e) the shares; (f) the secret images decrypted by stacked (d), (e) together; (g), (h) the phase keys; (i), (j) the reconstructed shares using (g), (h); (k) the recover secret images by stacking (i), (j) together
Fig. 7. Optical setup for the extraction process of EVCOH
Fig. 8. (a), (b) The shares, (c) the secret images decrypted by stacked (a), (b) together; (d), (e) the phase keys; (f), (g) the reconstructed shares that were taken with a CCD camera; (h) the recover secret images by stacking (f), (g) together
Fig. 9. Noise analysis of EVCOH
Fig. 10. Noise analysis of EVCOH when the phase keys are four steps
Set citation alerts for the article
Please enter your email address



