Cheng ZHANG, Hai-tao XU, Yuan-yuan ZHU, Jun TANG, Sui WEI. Multiple Color Images Encryption via Compressive Holography and Spatial Multiplexing[J]. Acta Photonica Sinica, 2020, 49(9): 0910001
Search by keywords or author
- Acta Photonica Sinica
- Vol. 49, Issue 9, 0910001 (2020)
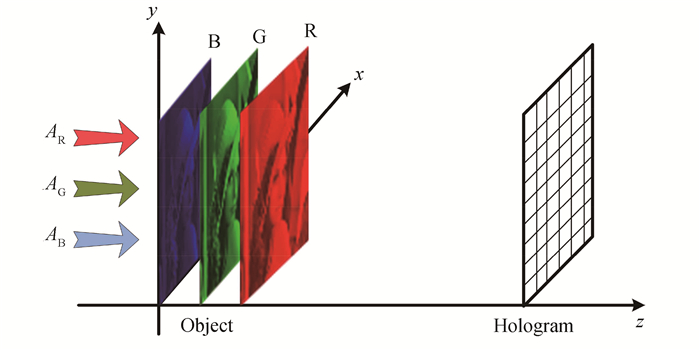
Fig. 1. Schematic diagram of compressive color holography
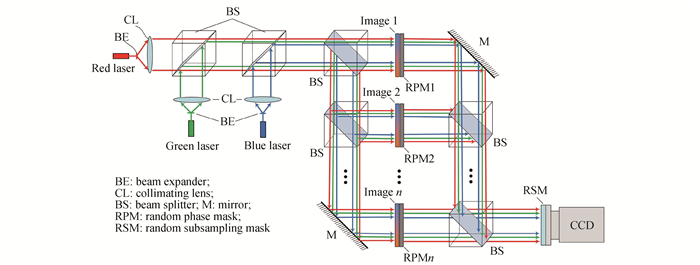
Fig. 2. Schematic setup of multiple color image encryption based on space division multiplexing
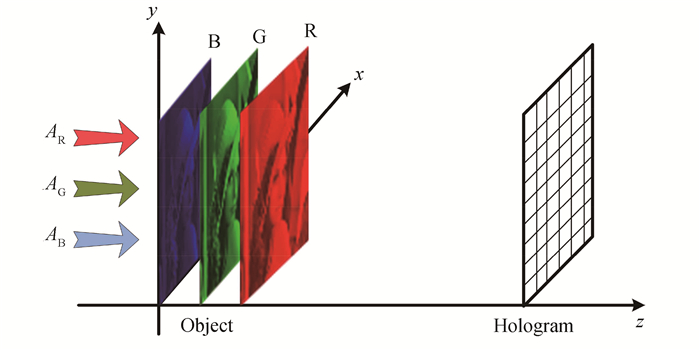
Fig. 3. Decryption model of multiple color image
Fig. 4. Flow chart of the proposed multiple color image encryption and decryption process
Fig. 5. Comparison of self-sparse color image with inherent noise
Fig. 6. Comparison of complex color image with inherent noise
Fig. 7. Comparison of self-sparse color image with encryption
Fig. 8. Comparison of complex color image with encryption
Fig. 9. The simulated results of encryption and decryption security on RPM
Fig. 10. The simulated results of encryption and decryption security on propagating distance
Fig. 11. The simulated results to investigate the robustness against occlusion attack (sampling ratio δ )
Fig. 12. Simulated results on the robust of decryption against Gaussian noise with the different standard deviation σ
|
Table 1. Definition of variables and description of dimensions
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Table 2. The performance comparison of color image with inherent noise
| ||||||||||||||||||||||||||||||||||||||||||
Table 3. The performance comparison of multiple self-sparse color image
| ||||||||||||||||||||||||||||||||||||||||||
Table 4. The performance comparison of multiple complex color image shown
|
Table 5. The performance comparison of occlusion attack
|
Table 6. The robust performance comparison of decryption under Gaussian noise
Set citation alerts for the article
Please enter your email address



