- Chinese Optics Letters
- Vol. 20, Issue 11, 110601 (2022)
Abstract
1. Introduction
To meet the increasing demand for underwater activities, such as ocean explorations and rescue missions, underwater wireless sensor networks (UWSNs)[
UWOC is customarily regarded as highly secure compared with UAC since the light source is highly directional and has limited penetration distance in common waters[
A UWOC system does not inherently provide a secure transmission link, making it easy for attackers to capture information. In seawater, especially for long-reach transmission, the scattering effect will make the received light spot much larger than the detection area, thereby increasing the risk of signal eavesdropping[
Sign up for Chinese Optics Letters TOC. Get the latest issue of Chinese Optics Letters delivered right to you!Sign up now
In this Letter, we present a security-enhanced orthogonal frequency division multiplexing (OFDM) scheme based on three-layer chaotic encryption and chaotic discrete Fourier transform (DFT) precoding in a UWOC system, which can simultaneously guarantee sufficiently high security and transmission performance. The application of multiple hyperchaotic maps and multi-fold data encryption can improve the key space and reduce the risk of the scrambling method and chaotic model being destroyed by statistical analysis. Multiple hyperchaotic maps generate masking factors, implementing bit stream diffusion encryption, in-phase/quadrature (IQ) encryption, time-frequency dimensional scrambling, and chaotic DFT precoding in OFDM. The chaotic DFT precoding matrix is generated to reduce the peak to average power ratio (PAPR) and bit error rates (BERs). The chaotic DFT precoding matrix is obtained by introducing chaotic sequences into the standard DFT matrix for phase encryption and column permutation. Hence, it is more difficult to crack than the encrypted DFT matrix in Refs. [18,19]. To verify the feasibility of the scheme, a 3 Gbit/s encrypted 16-quadrature amplitude modulation (16-QAM) OFDM signal is successfully demonstrated over a 7 m UWOC link. The encryption system is tested and analyzed to have higher security with a key space of
2. Principles
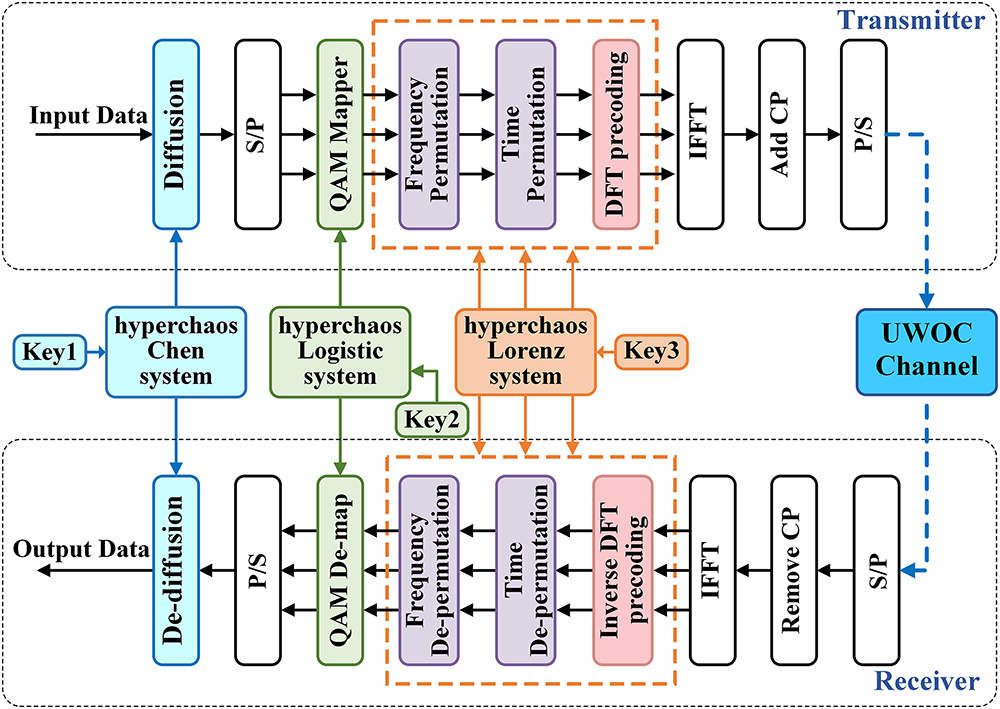
The concept of the proposed security-enhanced OFDM system for UWOC based on three-layer chaotic encryption and chaotic DFT precoding is shown in Fig. 1. The key-driven hyperchaotic maps are used to generate masking factors. It has been proved that signals encrypted by low-dimensional chaotic maps are not always safe[
![]()
Figure 1.Block diagram of the secure OFDM-UWOC based on three-layer chaotic encryption and chaotic DFT precoding.
2.1. Diffuse encryption
Bidirectional diffusion in cryptography makes each bit in the plaintext affect many bits in the ciphertext. Here, a four-dimensional (4D) hyperchaotic Chen system is applied to generate chaotic sequences for bidirectional diffusion[
When
The function
Step 2 can diffuse the plaintext into the ciphertext to different degrees but fails to spread globally due to the single direction of the diffusion, and the following plaintext cannot be diffused to the preceding ciphertext. Hence, using bidirectional diffusion, each part of the binary plaintext information is fully diffused into the ciphertext to generate an utterly dynamic ciphertext. When the plaintext is changed, the entire ciphertext will produce irregular changes, which can effectively resist the CPAs.
2.2. IQ encryption
Then, the first layer of encrypted data
The encryption for the
2.3. Time-frequency dimensional scrambling
After completing the IQ encryption in the second layer, the OFDM frames are scrambled in the time-frequency dimension[
![]()
Figure 2.Schematic diagram of time-frequency scrambling[
The data matrix after IQ encryption can be expressed as
Equation (9) defines the row vectors of the data matrix as
2.4. Chaotic DFT precoding
In this work, chaotic DFT precoding is adopted to reduce PAPR and increase the security of UWOC additionally[
According to the above equation, the standard DFT matrix of
Compared with other single and common chaotic mappings, the multiple hyperchaotic mappings used have more dimensions, leading to increased complexity and security of the UWOC encryption system, similar to the seven-dimensional (7D) chaotic mappings applied in Ref. [20]. However, once the encryption system is implemented in practical applications, we do not need to iterate multiple hyperchaotic systems or update the key sequence frequently until the key of the UWOC system changes. In this case, the major computation complexity would only come from the encryption at the system level[
| Our Scheme | Ref. [ | Ref. [ | |
|---|---|---|---|
| Real-valued multiplication | 0 | N2 | 0 |
| Complex-valued multiplication | M2 + N2 | M2 | M2 + N2 |
| Addition | M(M − 1) + N(N − 1) | 3M(M − 1) + 2M × (2M − 1) + N(N − 1) | M(M − 1) + N(N − 1) |
Table 1. The Computation Complexity of Encryption Schemes
| Our Chaotic Systems | 7D Chaos (Ref. [ | Chaos Maps (Ref. [ | |
|---|---|---|---|
| Addition | 104 | 221 | 5 |
| Multiplication | 110 | 118 | 10 |
| Sine function | 0 | 4 | 2 |
Table 2. The Computation Complexity of Chaos Systems
As mentioned above, there is a trade-off between security and complexity. It is worth mentioning that the UWOC encryption method in this Letter does not introduce any additional optical modules, and all of the encryption and decryption operations are performed in the digital signal processing (DSP), so the impact of the iterations of chaotic mapping is small[
3. Experimental Setup
The experimental setup of the proposed high-security OFDM system for UWOC based on three-layer chaotic encryption and chaotic DFT precoding is shown in Fig. 3. At the transmitter, the bit streams are encrypted and loaded into an arbitrary waveform generator (AWG, Tektronix 70002A) at a sampling rate of 3.125 GSamples/s. The voltage amplitude of the output signal is appropriately adjusted using an amplifier (AMP) and a variable electronic attenuator (ATT). Subsequently, the encrypted signal is superimposed on a bias tee (Bias-T) with a direct current (DC) of 0.3414 A, so that the drive signal operates within the linear region of the blue LD. The blue light is collimated by a collimating lens (CL) and emitted into a 7 m water tank filled with tap water. At the receiver, the blue light is incident on an avalanche photodiode (APD210) after passing through a focusing lens (FL) and a variable optical ATT (VOA). Finally, the detected encrypted signals are captured via a mixed signal oscilloscope (MSO, Tektronix MSO71254C) at a sampling rate of 25 GSamples/s and processed offline by a personal computer (PC). The final data transmission rate is about 3 Gbit/s. Table 3 shows the detailed OFDM parameters of the UWOC system.
| OFDM Parameters | Values |
|---|---|
| Modulation format | 16-QAM |
| Number of effective subcarriers | 256 |
| Inverse fast Fourier transform (IFFT) size | 1024 |
| Number of cyclic prefix (CP) | 64 |
| Number of subcarriers for gap near DC | 8 |
| Number of OFDM symbols | 520 |
Table 3. Parameters of the OFDM-UWOC System
![]()
Figure 3.Experimental setup. Insets: (a) the transmitter module, (b) the water tank, and (c) the receiving module.
4. Performance and Safety Analysis
The PAPR and BER are utilized to evaluate the performance of our encryption scheme. Besides, image transmission is a typical digital communication application, so we tested the encryption scheme with image data to visualize the encryption performance. The complementary cumulative distribution functions (CCDFs) of PAPRs for the original and encrypted data are shown in Fig. 4.
![]()
Figure 4.Performance of PAPR for (a) original image data and (b) three-layer encrypted data under different conditions.
The PAPR decreases along with the auto-correlation coefficient of the input data reduction before the N-IFFT operation[
![]()
Figure 5.BER curves of normal and illegal receiver for (a) original image data and (b) three-layer encrypted data.
It can be further verified that our scheme can be used in UWOC with high confidentiality and solid BER performance. Figure 5 shows BER curves and constellation diagrams of the original image and the encrypted data. The legal receiver can correctly recover the data using the correct private key. In contrast, illegal receivers always obtain a BER of about 0.5 and cannot decrypt the message, even if they obtain most of the correct key, with only a slight difference of
The randomness of chaotic systems and their high sensitivity to initial conditions are the basis of our encryption algorithm. Multiple hyperchaotic mappings can create a larger key space and increase the difficulty for attackers to crack. According to the Institute of Electrical and Electronics Engineers (IEEE) floating-point standard[
It is worth noting that two-layer encryption without diffusion has a better BER performance than three-layer encryption in Fig. 5(b). Owing to the XOR operation in the diffusion, which associates the front and back plaintexts, noise accumulation will happen when the ciphertext is decrypted. However, diffusion encryption can generate dynamic ciphertexts to resist the most threatening and aggressive CPAs, so the performance penalty is acceptable. In this paper, to obtain higher information security and ensure transmission performance, chaotic DFT precoding is adopted to compensate for the loss, even improving the reception sensitivity by about 1 dB.
To verify the anti-CPA ability of our encryption system, we give the variations of the ciphertext when changing 1 bit of the plaintext, as shown in Fig. 6. The 10th bit of the original binary plaintext has been changed in Fig. 6(a). Figure 6(b) indicates great difference between the new ciphertext obtained after the corresponding plaintext change and the original one in the same OFDM subcarrier, implying that the plaintext information has been sufficiently spread out to nearly all the data during the ciphertext generation process in the OFDM-based UWOC system. For clarity, Fig. 6(b) only shows the difference of ciphertext change on the first 60 OFDM subcarriers. Consequently, the proposed encryption system can mix up the relationship between the original data and the ciphertext to resist CPAs.
![]()
Figure 6.(a) Change 1 bit in plaintexts. (b) The difference of ciphertext change on the first 60 OFDM subcarriers.
5. Conclusion
In this Letter, we have proposed a security-enhanced OFDM scheme for UWOC using three-layer chaotic encryption and chaotic DFT precoding. Although there is a trade-off between security and system complexity, the experiment in this paper validates the transmission performance and feasibility of this scheme, which is also an additional way to achieve UWOC secure transmission. The three-layer encryption operations of OFDM symbols are diffusion, IQ encryption, and time-frequency scrambling in turn. Finally, chaotic DFT precoding compensates for BER deterioration, and the key space reaches
References
[1] A. Khasawneh, M. S. Bin Abd Latiff, O. Kaiwartya, H. Chizari. Next forwarding node selection in underwater wireless sensor networks (UWSNs): techniques and challenges. Information, 8, 3(2016).
[2] M. Kong, J. Wang, Y. Chen, T. Ali, R. Sarwar, Y. Qiu, S. Wang, J. Han, J. Xu. Security weaknesses of underwater wireless optical communication. Opt. Express, 25, 21509(2017).
[3] S. Jiang. On securing underwater acoustic networks: a survey. IEEE Commun. Surv. Tutor., 21, 729(2019).
[4] Y. Huang, C. Tsai, Y. Chi, D. Huang, G. Lin. Filtered multicarrier OFDM encoding on blue laser diode for 14.8-Gbps seawater transmission. J. Light. Technol., 36, 1739(2018).
[5] J. Wang, C. Lu, S. Li, Z. Xu. 100 m/500 Mbps underwater optical wireless communication using an NRZ-OOK modulated 520 nm laser diode. Opt. Express, 27, 12171(2019).
[6] J. Lin, Z. Du, C. Yu, W. Ge, W. Lü, H. Deng, C. Zhang, X. Chen, Z. Zhang, J. Xu. Machine-vision-based acquisition, pointing, and tracking system for underwater wireless optical communications. Chin. Opt. Lett., 19, 050604(2021).
[7] M. Gao, C. Li, Z. Xu. Performance enhancement of LED-based indoor OFDM-VLC system using digital chaotic scheme. Opt. Commun., 439, 21(2019).
[8] D. Shaboy, D. Rockban, A. Handelman. Tapping underwater wireless optical communication in pure water and natural dead-sea ultra-high-salinity water by diffraction grating. Opt. Express, 26, 29700(2018).
[9] G. Baiden, Y. Bissiri, A. Masoti. Paving the way for a future underwater omni-directional wireless optical communication systems. Ocean Eng., 36, 633(2009).
[10] X. Sun, M. Kong, O. A. Alkhazragi, K. Telegenov, M. Ouhssain, M. Sait, Y. Guo, B. H. Jones, J. S. Shamma, T. K. Ng, B. S. Ooi. Field demonstrations of wide-beam optical communications through water-air interface. IEEE Access, 8, 160480(2020).
[11] X. Sun, W. Cai, O. Alkhazragi, E.-N. Ooi, H. He, A. Chaaban, C. Shen, H. M. Oubei, M. Z. M. Khan, T. K. Ng, M.-S. Alouini, B. S. Ooi. 375-nm ultraviolet-laser based non-line-of-sight underwater optical communication. Opt. Express, 26, 12870(2018).
[12] X. Sun, M. Kong, O. Alkhazragi, C. Shen, E. N. Ooi, X. Zhang, U. Buttner, T. K. Ng, B. S. Ooi. Non-line-of-sight methodology for high-speed wireless optical communication in highly turbid water. Opt. Commun., 461, 125264(2020).
[13] Y. Chen, W. G. Shen, Z. M. Li, C. Q. Hu, Z. Q. Yan, Z. Q. Jiao, J. Gao, M. M. Cao, K. Sun, X. M. Jin. Underwater transmission of high-dimensional twisted photons over 55 meters. PhotoniX, 1, 5(2020).
[14] S. Zhao, W. Li, Y. Shen, Y. H. Yu, X. H. Han, H. Zeng, M. Cai, T. Qian, S. Wang, Z. Wang, Y. Xiao, Y. Gu. Experimental investigation of quantum key distribution over water channel. Appl. Opt., 58, 3902(2019).
[15] L. Ji, J. Gao, A.-L. Yang, Z. Feng, X.-F. Lin, Z.-G. Li, X.-M. Jin. Towards quantum communications in free-space seawater. Opt. Express, 25, 19795(2017).
[16] J. Zhang, G. Gao, B. Wang. Spectrum spreading and encryption of underwater optical OFDM communication. Asia Communications and Photonics Conference/International Conference on Information Photonics and Optical Communications (ACP/IPOC), M4A.284(2020).
[17] Y. Shang, W. Mao, M. Han, C. Xu, G. Gao. Underwater wireless optical communication with high modulation level based stream cipher. Asia Communications and Photonics Conference (ACP), Su2A.247(2018).
[18] J. Du, Y. Wang, C. Fei, R. Chen, G. Zhang, X. Hong, S. He. Experimental demonstration of 50-m/5-Gbps underwater optical wireless communication with low-complexity chaotic encryption. Opt. Express, 29, 783(2021).
[19] Z. Shen, X. Yang, H. He, W. Hu. Secure transmission of optical DFT-S-OFDM data encrypted by digital chaos. IEEE Photon. J., 8, 7904609(2016).
[20] Z. Hu, C. K. Chan. A 7-D hyperchaotic system-based encryption scheme for secure fast-OFDM-PON. J. Light. Technol., 36, 3373(2018).
[21] M. Bi, X. Fu, X. Zhou, L. Zhang, G. Yang, X. L. Yang, S. Xiao, W. Hu. A key space enhanced chaotic encryption scheme for physical layer security in OFDM-PON. IEEE Photon. J., 9, 7901510(2017).
[22] B. Liu, L. Zhang, X. Xin, Y. Wang. Physical layer security in OFDM-PON based on dimension-transformed chaotic permutation. IEEE Photon. Technol. Lett., 26, 127(2014).
[23] T. Wu, C. Zhang, H. Wei, K. Qiu. PAPR and security in OFDM-PON via optimum block dividing with dynamic key and 2D-LASM. Opt. Express, 27, 27946(2019).
[24] D. Chen, D. Qing, D. Wang. AES key expansion algorithm based on 2D logistic mapping. Fifth International Workshop on Chaos-fractals Theories and Applications, 207(2012).
[25] G.-Y. Wang, Y. Zheng, J.-B. Liu. A hyperchaotic Lorenz attractor and its circuit implementation. Acta. Phys. Sin., 56, 3113(2007).
[26] Z. Hu, P. Song, C. K. Chan. Chaotic non-orthogonal matrix-based encryption for secure OFDM-PONs. IEEE Photon. Technol. Lett., 33, 1127(2021).
[27] R. Tang, B. Liu, Y. Mao, R. Ullah, J. Ren, X. Xu, J. Zhao, M. Li, S. Chen, Y. Han. High security OFDM-PON based on an iterative cascading chaotic model and 4-D joint encryption. Opt. Commun., 495, 127055(2021).
[28] . Standard for binary floating-point arithmetic(1985).
Set citation alerts for the article
Please enter your email address



