Baoqing Sun, Yupeng Wang. Temporal Ghost Imaging and Its Application[J]. Chinese Journal of Lasers, 2021, 48(12): 1212001
Search by keywords or author
- Chinese Journal of Lasers
- Vol. 48, Issue 12, 1212001 (2021)
![Comparison of classical spatial and temporal GI experimental set-ups[26]. (a) Spatial set-up; (b) temporal set-up](/richHtml/zgjg/2021/48/12/1212001/img_1.jpg)
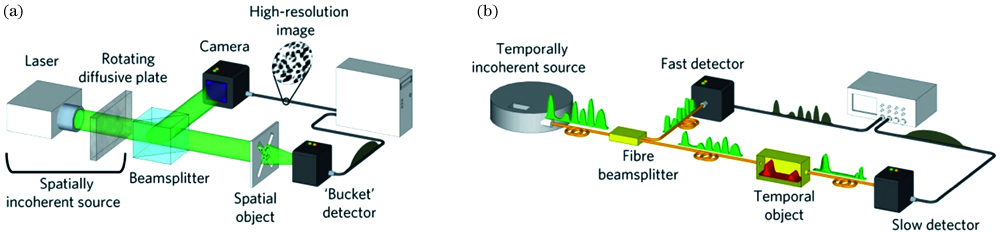
Fig. 1. Comparison of classical spatial and temporal GI experimental set-ups[26]. (a) Spatial set-up; (b) temporal set-up
![Experimental results temporal ghost imaging[26]. (a) Comparison of temporal ghost imaging and direct imaging measured with the fast detector; (b) comparison of temporal ghost imaging and direct imaging when a multimode fiber is added between the object and the detector](/richHtml/zgjg/2021/48/12/1212001/img_2.jpg)
Fig. 2. Experimental results temporal ghost imaging[26]. (a) Comparison of temporal ghost imaging and direct imaging measured with the fast detector; (b) comparison of temporal ghost imaging and direct imaging when a multimode fiber is added between the object and the detector
Fig. 3. Schematic diagram of intensity-only detection computational temporal ghost imaging[31]
Fig. 4. Experimental results of intensity-only detection computational temporal ghost imaging[31]
Fig. 5. Schematic diagram of thermal temporal ghost imaging[32]
Fig. 6. Experimental results of thermal temporal ghost imaging(insert: the transmission spectrum of the bandwidth-variable tunable filter)[32]
Fig. 7. Schematic diagram of magnified time-domain ghost imaging[27]
Fig. 8. Experimental results of magnified time-domain ghost imaging[27]
Fig. 9. Experimental setup for temporal ghost imaging with wavelength conversion[34]
Fig. 10. Experimental ghost image of temporal objects[34]. (a) and (b) are two examples of different bit sequences (The solid lines represent the ghost image; the dashed lines correspond to the direct measurement results with the 2 μm fast detector)
Fig. 11. Experimental setup for detecting a temporal signal via computational temporal ghost imaging[42]
Fig. 12. Comparison of results of direct detection and computational temporal GI[42]. (a) Bandwidth is 10 MHz; (b) bandwidth is 1 MHz; (c) bandwidth is 300 kHz; (d) bandwidth is 100 kHz; (e) bandwidth is 10 kHz; (f) bandwidth is 1 kHz
Fig. 13. Schematic diagram of VLC encryption and decryption process based on computational temporal ghost imaging[53]
Fig. 14. Experimental results of communication security scheme based on computational temporal ghost imaging[53]
Fig. 15. Schematic diagram of spatial multiplexing computational temporal ghost imaging[58]
Fig. 16. Algorithmic framework of the encryption scheme based on spatial multiplexing computational temporal ghost imaging[46]. (a) Encryption procedure; (b) decryption procedure
Fig. 17. Experimental results of the security scheme[46]. (a) Original image to be encrypted; (b) one binary random pattern of the secret key sequence; (c) image after encrypted; (d) reconstructed image with correct key; (e) decrypted image using the key with completely different spatial distribution; (f) decrypted image using wrong order of the key
Fig. 18. Experimental results of robustness testing[46]. (a) Encrypted image with 25% occlusion; (b) reconstructed image by the incomplete ciphertext; (c) ciphertext after adding zero-mean white additive Gaussian noise; (d) reconstructed image by the ciphertext with noise; (e) decrypted image using 20% patterns in proper order; (f) decrypted image using the right secret key but without demodulation of ciphertext when additional modulation on the ciphertext is introduced
Fig. 19. Camera acquisition process of the high speed imaging scheme[68]
Fig. 20. Results of image recovery[68]. (a) Rotating Rubik’s Cube taken by the camera directly; (b) reconstruction of 64 frames of images based on spatial multiplexing computational temporal ghost imaging
Set citation alerts for the article
Please enter your email address



